Chapter 4. Configuration and customization 167
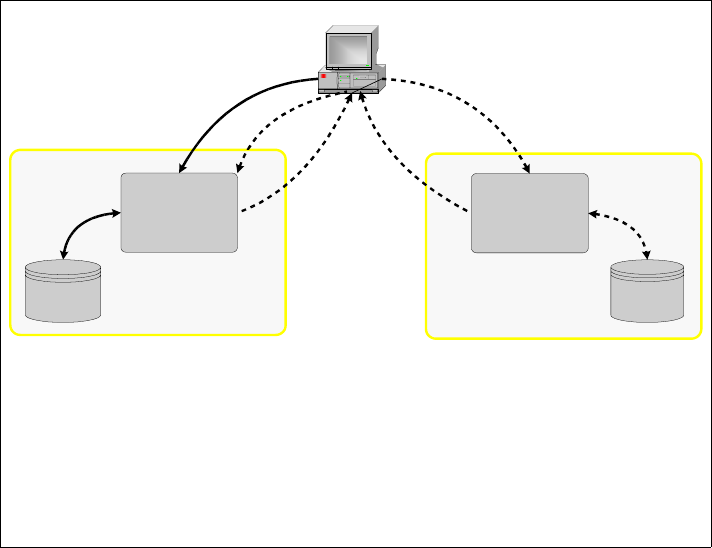
4.10.2 Cross-domain single sign-on
WebSEAL supports the ability to forward an authenticated identity from a user in
one secure domain to a WebSEAL server in another secure domain. The
receiving WebSEAL then maps the identity provided by the sending WebSEAL to
an identity that is valid in its secure domain. This functionality can also be viewed
as a
push model with respect to authentication.
This functionality is known as cross-domain single sign-sn (CDSSO). In CDSSO,
the user makes a request to a special link on a WebSEAL server, which then
initiates the process to forward the request, along with credential information, to
a WebSEAL server in a different Access Manager domain. If the user were to
instead directly access the link in the target domain, he would have to
authenticate to that domain.
The CDSSO process includes the following steps:
1. A user initially logs on to a WebSEAL server in one secure domain.
2. At some point the user accesses a link controlled by the user’s WebSEAL,
which contains a special directive (pkmscdsso). This directive results in
redirecting the user to a URL controlled by a WebSEAL server in another
secure domain and passing encrypted credential information to the new
WebSEAL.
3. The user is redirected to the other WebSEAL and this server decrypts the
credential information passed to it, maps the identity to one defined in its own
user registry, and then creates a secure session with the browser.
4. At this point the user has established secure sessions with two WebSEAL
servers in different domains, but has only had to log in once.
The tokens are encrypted using triple-DES. The symmetric key is generated by
the cdsso_key_gen utility and exchanged between all WebSEALS that
participate in CDSSO.
Another way of looking at CDSSO is that it provides a mechanism by which a
WebSEAL server in one secure domain can send something analogous to a
letter of introduction to a WebSEAL server in another secure domain.
Note: Cross-domain single sign-on requires that the back-end application is
aware of this functionality existing. It is required to generate the appropriate
URL when forwarding the request to another domain. If back end changes to
an application are not permitted or desired, or if application awareness of
WebSEAL’s single sign-on functionality is not possible, then e-community
single sign on should be used. See 4.10.3, “e-community single sign-on” on
page 169 for more information.