In this recipe we will remotely elevate privilege on a Linux device:
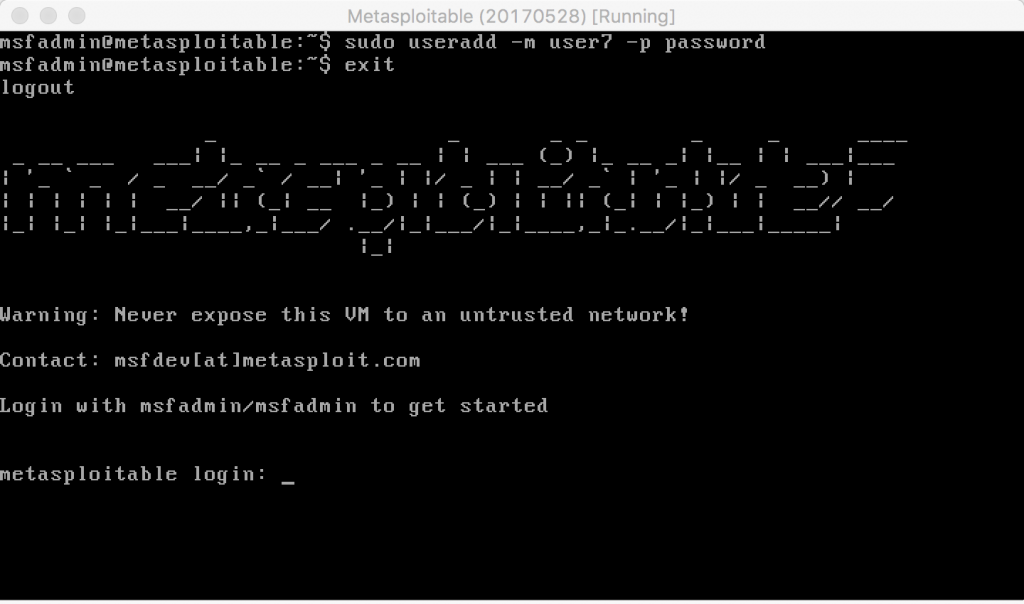
- First, let's log in to the Metasploitable VM and add a standard user.
- From the console, enter the following commands to add a user and validate the IP address of the Metasploitable host:
cd <enter>ifconfig <enter>sudo useradd -m user7 <enter> msfadmin <enter>exsudo passwd user7 <enter> password <enter> password <enter>exit <enter>
- From Kali, let's start Armitage.
- From Armitage, ...

