Introduction
And you may ask yourself, “Well, how did I get here?”
Talking Heads, “Once in a Lifetime”
Why Are We Here?
This report grew out of a series of “lunch-and-learns” on Linux that I compiled for work. During that process, I ended up writing an ebook, and then condensing it into a one-hour presentation that focuses on the essentials needed for quick problem-solving on a Linux system. I turned that presentation into an O’Reilly webcast, and this report provides more details on those original 10 essentials.
Even in formerly “pure Windows” shops, Linux use is growing. Linux systems are everywhere! They may appear as appliances (machines) or, more likely, virtual machine (VM) images dropped in by a vendor.
Common examples of Linux systems that may appear in your shop as VMs or in the cloud include the following:
- Web servers
-
Apache, Nginx, Node.js
- Database servers
-
MongoDB, PostgreSQL
- Mobile device management
-
Various MDM solutions, such as MobileIron
- Security and monitoring systems
-
Security information and event management (SIEM) systems, network sniffers
- Source-code control systems
-
Git or Mercurial
As Linux use continues to grow, you need to know the basics. One day you might be the only one in the office when things go south, and you’ll have to fix them—fast. This guide will help.
In this report, I focus on diagnosing problems and getting a system back up. I don’t cover these topics:
-
Modifying the system, other than restarting
-
Forensics, other than looking at logs
-
Shell scripting
-
Distro differences—for example, Ubuntu versus CentOS
-
Anything in depth, as this is just to get your feet wet
Who Is This For?
The intended audience of this book is not seasoned Linux administrators, or anyone with a passing knowledge of the Bash shell. Instead, it is for people who are working in small Windows shops, where everyone has to wear various hats. It is for Windows administrators, network admins, developers, and the like who have no knowledge of Linux but may still have to jump in during a problem. Imagine your boss rushing into your office and saying this:
The main www site is down, and all the people who know about it are out. It’s running on some sort of Linux, I think, and the credentials and IP address are scrawled on this sticky note. Can you get in, poke around, and see if you can figure it out?
In this report, you’ll learn the basic steps to finding vital information that can help you quickly get the site back up. By reading this guide before disaster strikes, you will be better able to survive the preceding scenario.
How to Prepare
In small shops, sometimes things just fall on you because no one else is available. There is often no room for “It’s not my job” when production is down and the one person who knows about it is backpacking in Colorado. So you need to be prepared as the use of Linux becomes more prevalent, turning “pure Microsoft” shops more and more into hybrids. Linux is coming, whether you like it or not. Be prepared.
First, pay close attention whenever you hear the word appliance used in terms of a system. Perhaps it will be mentioned in passing in a vendor presentation. Dig in and find out what the appliance image is running.
Second, note that even Microsoft is supporting Linux, and increasing that support daily. First, it started with making Linux systems first-class citizens on Azure. Now Microsoft is partnering with Docker and Ubuntu and others, and that coordination looks like it is only going to grow.
So now is the time to start studying. This report is a quick-help guide to prepare you for limited diagnostic and recovery tasks, and to get you used to how Linux commands work. But you should dig further.
One place to turn next is my ebook. It helps you take the next steps of understanding how to change Linux systems in basic ways. I’ve also included some useful references at the end of this report. Past that, obviously, O’Reilly has many good resources for learning Linux. And the Internet is just sitting there, waiting for you.
Play with It!
The best way to learn Linux is to stand up an environment where you can explore without fear of the consequences if you mess something up. One way is to create a Linux VM; even a moderately provisioned modern laptop will comfortably run a Linux VM. You can also create one in the cloud, and many vendors make that easy, including DigitalOcean, Linode, Amazon Elastic Compute Cloud (EC2), Microsoft Azure, and Google Compute Engine. Many of these even offer a free level, perfect for playing!
Documentation and Instrumentation
To protect yourself in case you are thrown into the scenario outlined at the beginning of this report, you should make sure the following are in place at your shop:
- The Linux systems are documented.
-
This should include their purpose, as-built documentation outlining the distro, virtual or physical hardware specs, packages installed, and so on.
- These systems are being actively monitored.
-
Are they tied in to Paessler Router Traffic Grapher (PRTG), SIEM, and other monitoring and alerting systems? Make sure you have access to those alerts and monitoring dashboards, as they can be a great source of troubleshooting information.
- You have access to the system credentials.
-
Ideally, your department uses secure vault software to store and share system credentials. Do you have access to the appropriate credentials if needed? You should make sure before the need arises.
Conventions
If a command, filename, or other computer code is shown inline in a sentence, it appears in a fixed-width font:
ls --recursive *.txt
If a command and its output is shown on a terminal session, it appears as shown in Figure P-1.
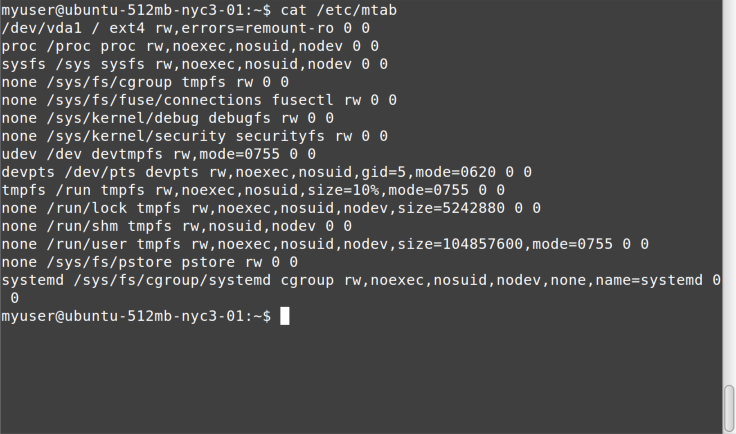
Figure P-1. cat command
All such blocks have been normalized to show a maximum of only 80 x 24
characters. This is intentional. Although most modern Linux systems and
terminal windows such as ssh can handle any geometry, some
systems and situations still give you the same terminal size that your
grandfather would’ve used. It is best to learn how to deal with these by
using less, redirection, and the like. In addition, screenshots are shown from a variety of systems, to get you used to the ways that command
output and terminal settings can differ, much more than under the
default Windows Command Prompt.
The examples in this book typically show something like
myuser@ubuntu-512mb-nyc3-01:~ $ before the command (as in the previous
example). In other systems, you may simply see ~ # (when logged in as
root) or % (when running under csh). These command prompts are not
meant to be typed in as part of the command. Although they may seem
confusing in the samples, you need to get used to looking at a
terminal and “parsing” what is being displayed. And in our scenarios,
you won’t have control over the command prompt format. Get used to it.
Typically, the screenshots are set up with the command entered at the prompt at the top of the screen, the command output immediately following, and in most cases a new command prompt waiting for another command at the end, as in the preceding example.
In the few places, where a Linux command is shown in comparison to a DOS
command run under Windows Command Prompt, the latter is shown in all uppercase to
help distinguish it from the Linux equivalent, even though Windows Command Prompt is
case-insensitive. In other words, cd temp is shown for bash, and
CD TEMP for CMD.EXE.
This element signifies a tip or suggestion.
This element signifies a general note.
This element indicates a warning or caution.
Get Ten Steps to Linux Survival now with the O’Reilly learning platform.
O’Reilly members experience books, live events, courses curated by job role, and more from O’Reilly and nearly 200 top publishers.

