� March 2005 | Main | May 2005 �
April 29, 2005
Spammers Can't Hide Behind Affiliates
 Microsoft is proving that persistence pays off in the legal battle against spam.
Microsoft is proving that persistence pays off in the legal battle against spam.
As I report today in a new article for O'Reilly Network, Microsoft has scored a legal victory against Robert Soloway and his company, Newport Internet Marketing, alleged by Spamhaus to be one of the top ten spam operations in the world.
A King County (Washington) superior court judge awarded Microsoft a default judgment in the suit, originally filed December 18, 2003. Soloway had tried to dance around the complaint, placing blame on spam affiliates. But the court reaffirmed a key provision in CAN-SPAM and in Washington State's spam statute: You don't have to push the send button to be liable for illegal spam.
We'll have to wait for the dust to settle on this one, not to mention on the Richter lawsuit. (Soloway offered me this provocative if puzzling quote: "They have no case, and I can honestly say with the utmost confidence that there will not be a monetary damage awarded.")
But if Microsoft comes through, I may have to change my opinion about how Bill Gates is losing the war on spam.
(BTW, that pic above is of Microsoft's top spam lawyer, Aaron Kornblum. Soloway declined to provide a photo.)
Posted by Brian at 7:00 PM | Comments (3)
April 28, 2005
Spyware deja vu
 NY State's lawsuit against alleged spyware maker Intermix will be fun to watch.
NY State's lawsuit against alleged spyware maker Intermix will be fun to watch.
TheStreet.com has an interesting story about how the suit catches Intermix in the midst of what it hoped was a financial turnaround.
For me, the news provided a strange moment of double deja vu.
Intermix used to be called eUniverse, which was the parent company of CD Universe, the online music store that was blackmailed in 2000 by a Russian hacker named Maxus. I interviewed Maxus via email after he started giving away credit card numbers he had stolen from CD Universe.
EUniverse also operated the Flowgo.com site, which was indirectly responsible in 2002 for infecting thousands of visitors with a malicious program called Downloader-W. I wrote a story about the incident for Salon, and then followed up with a piece about the mysterious creators of the malware, a company called Intellitech, which was run by a couple of very strange dudes said to be hopped up on steroids.
Oddly, just yesterday I received an email from an executive with a company about to enter into a joint venture with one of the founders of Intellitech. The exec wondered if I had any recent impressions of the Intellitech founder.
Hmm. I guess my overall impression is that spyware companies, like the software they create, are darn hard to eradicate.
Posted by Brian at 9:41 PM
April 27, 2005
Hotmail goes anonymous?
![]() Is Microsoft's Hotmail service making it harder to track spammers?
Is Microsoft's Hotmail service making it harder to track spammers?
It has come to my attention that Hotmail often does NOT include the user's Internet protocol (IP) address in outbound email messages.
I'm not sure whether this change is just a temporary, non-systemwide thing that doesn't affect all accounts. But removing this tracking information seems like a significant move backwards in trying to control spam and other abuse of Hotmail's service.
In the past, Hotmail always included the user's IP address in a header called X-Originating-IP. As spam expert John Levine noted to me, including the user's IP is a good idea for a variety of reasons. First, it gives recipients some power to track who's emailing them. Including the sender's IP also makes reporting spam and abuse much easier, and it also aids in spam filtering.
But in my (limited) testing, Hotmail now often lists its own (Microsoft) IP addresses in the X-Originating-IP spot. (Hotmail reliably seems to include the sender's IP address on emails sent to other Hotmail users.)
Has anyone else noticed this behavior by Hotmail? What do you think? (Hotmail users: please send me a test message from your Hotmail account.)
Among the major webmail providers, Google's Gmail service was previously the only one that didn't include the user's IP. Google presumably does this to protect the user's privacy. According to Levine, Google has "some whizzo scheme in the works" to stop Gmail spam.
(Thanks to Kevin Beck, editor of Run Strong, for the tip.)
[UPDATE: spamfighter J.D. Falk writes to say, "I've heard from an extremely reliable source at Hotmail that this is an artifact of some new load-balancing equipment, and they're working on changing things to return to the previous functionality. As usual, there's no implicitly evil intent involved." Whew.]
Posted by Brian at 10:46 AM | Comments (5)
April 26, 2005
AOL lands on spam blacklist
 If you're an AOL user and your emails aren't reaching their recipients today, chances are you've been blacklisted.
If you're an AOL user and your emails aren't reaching their recipients today, chances are you've been blacklisted.
In response to a handful of recent spam runs, Mail Abuse Prevention Systems (MAPS) has placed a large swath of AOL mail servers on the venerable MAPS Real-time Blackhole List (RBL).
The AOL listing at the MAPS site shows that eight IP ranges have been blacklisted -- affecting many of the systems that deliver AOL members' outbound mail.
According to Kalkea, the company that acquired MAPS last year, the RBL blacklist is used by some of the biggest ISPs in the world, including RoadRunner, USA.net, BT, Telstra -- and AOL itself.
The action by MAPS appears to have been prompted in part by several spam runs somehow relayed through AOL's mailservers on behalf of a pill site named simple-meds.com.
Samples of the spams show they are the work of "Vron," the alias of a prolific spammer who is an affiliate for BlackmarketMoney.com -- the spam affiliate network I wrote about last year for Salon. You can spot Vron's affiliate ID in the URL of the millions of spams he has sent out in the past months.
MAPS' action is bound to generate some complaints, especially since it apparently began blocking AOL's servers less than 24 hours after initially filing a warning to the big ISP.
The rise of MAPS is covered in chapter six of Spam Kings.
[UPDATE: Looks like MAPS changed its mind. As of Tuesday afternoon ET (GMT -4:00), AOL's listing at the MAPS site is gone, and a lookup shows AOL's mail servers no longer seem to be on the MAPS RBL list. No word yet on whether AOL resolved the spam problems, or if MAPS just decided to give AOL more time.]
Posted by Brian at 9:59 AM | Comments (19)
April 20, 2005
No more refills for pill spammers?
 Spammers who market prescription drugs may find their suppliers are hard to reach as of today.
Spammers who market prescription drugs may find their suppliers are hard to reach as of today.
The US Drug Enforcement Administration (DEA) said it has busted up a major India-based pharmacy that was illegally selling Vicodin, steroids, amphetamines, and other controlled drugs over the Internet.
The head of the drug ring, Dr. Brij Bhushan Bansal, was reportedly picked up at his home in Agra, India, yesterday. His son, Temple University healthcare-management grad student Akhil Bansal, was arrested in Philadelphia.
The DEA said a total of 20 people were arrested worldwide. Besides the Bansals and their employees, the sweep netted several North American affiliates and distributors who submitted orders to Bansal organization.
According to the indictment, the distributors included:
KEVIN ATKINSON (operator of performancemarketingltd.com); VICTOR DEVORE (operator of bigcitymeds.com, greentreerx.com, mercomeds.com, rxapproved.com, and rxglobally.com); TOM PETERS and KELLY ANN COUCHMAN (operators of myemeds.com); MATTHEW JOSEPH MELAO and CHRISTOPHER GEOFF LAINE (operators of ourprescriptionsforless.com and yourpharmacyone.com); ROHN WALLACE (operator of usarxpress.com and discountmedsonline.com; WILLIAM RANDALL REED, a/k/a �millerlight�; and RICHARD DABNEY
Despite the arrests, all of the pharmacy sites listed above were still live Wednesday afternoon. So was OrdersPanel.com, the site they used to place orders with the Bansals.
Pills are currently one of the most heavily spammed items. It will be interesting to see whether this action results in some relief from all the "pharma" spam.
Posted by Brian at 4:23 PM | Comments (1)
April 18, 2005
Peer-to-peer email harvesting
 A provocative press release today warns of peer-to-peer (P2P) networks as a potential spam-harvesting threats.
A provocative press release today warns of peer-to-peer (P2P) networks as a potential spam-harvesting threats.
California-based Blue Security said it did some searches on the Gnutella P2P network and discovered lots of people were unknowingly sharing their Microsoft Outlook data files and other sources of email addresses.
To check it out, I went onto Gnutella and, sure enough, I was quickly able to scare up a couple copies of Outlook.pst and some text and Word documents containing email address lists from my fellow file-sharers.
Thing is, I'm not sure this is really much easier or productive than what spammers are currently doing to build their email lists. (I believe PST files are password protected, so that's an obstacle.)
As for the dangers to P2P users, if you're sharing PST files, you're probably in a heap of trouble, and not just spam-related. Chances are you're sharing the contents of your entire hard disk, rather than just a music folder and mp3 files.
Some folks have been known to unintentionally expose all sorts of private data (passwords, account numbers, etc.) via their use of P2P programs. Bad guys even take advantage of other peoples' snooping by creating documents with names like sexsitepasswords.doc which are actually just ads for porn sites.
Bottom line: this is another good reason to make sure you configure your P2P program with care. But I can't really see P2P harvesting as a huge threat.
Blue Security's announcement conveniently comes a couple weeks after the company received $3M in venture financing from Benchmark Capital.
Posted by Brian at 9:06 PM | Comments (1)
Lawsuit over coffee spam
![]() Did Gevalia sell its opt-out list to spammers?
Did Gevalia sell its opt-out list to spammers?
That's the allegation in an $11M lawsuit filed today against the coffee company, which is a unit of the Kraft food giant.
California ISP Hypertouch sued Gevalia under the CAN-SPAM act. President and founder Joe Wagner claims he submitted a new, unused email address to Gevalia's opt-out page, and soon began receiving spam at the new account.
Others have recently reported similar results with the opt-out page.
Gevalia has been publicly criticized for years over its use of spamming affiliates.
My hunch is that Gevalia distributed the "remove list" to its spamming affiliates, with instructions to scrub the addresses from their mailing lists. But some of the affiliates apparently turned around and treated it like an opt-in list.
In any case, Gevalia's in a lot of hot water (replace with your favorite coffee pun).
Last December, Hypertouch sued an alleged diploma mill for spamming.
Posted by Brian at 4:26 PM
April 16, 2005
Containing spam at the source
More curmudgeonly grumbling about spam in the media ...
I was intrigued by a recent story from the Associated Press that boldly begins: "There's a new strategy in the spam battle: Call it containment."
I'm all ears at that point, hoping the article will draw attention to the fact that zombied Windows computers are the primary conduit for spam. Maybe the exposure will encourage some consumers to take better care of their computers (patching, anti-virus software, etc) so they won't become zombified. Maybe the article will even spur broadband ISPs to be more proactive about helping infected customers, or even unplugging them from the Net.
But then the article goes on to talk about how AOL and Earthlink are taking steps to prevent people from sending spam from their mail servers. (Hotmail is also briefly mentioned, as are a few other ISPs.)
The story just blows right by a key statement from AOL's Carl Hutzler: that spam zombies are responsible for 90 percent of the junk email problem.
OK, so never mind AOL and Earthlink. What are ISPs like Comcast and Kornet -- home to many of the world's spam zombies -- doing lately to contain the problem?
The article doesn't even talk about attacking the zombie issue.
In the end, good PR for AOL and Earthlink (including a nice server-room photo of an Earthlink director). But a missed opportunity to stop spam before it's sent.
Posted by Brian at 10:53 PM | Comments (1)
April 15, 2005
Could spam die?
![]() Interesting spam commentary at USA Today by Cyberspeak columnist Andrew Kantor.
Interesting spam commentary at USA Today by Cyberspeak columnist Andrew Kantor.
Kantor speculates that spam will soon die out. The reason? Kantor's logic is a bit complex, but it boils down to a prediction that merchants are going to stop hiring spammers to advertise for them.
I wish Kantor's soothsaying was on the mark. But there are a couple of flaws in his assumptions about the spamming business. Specifically, he's incorrect in believing that spammers are primarily paid just to get people to read their messages (as opposed to receiving a commission from sales generated by the spam).
I emailed Kantor with my take on his article, and he posted my response at his personal site. Here's my answer to his article's question about why spammers work so hard to slip past filters:
Why are they marketing to people who seem not to want their messages? Remember, spammers are sales people, just like the door-to-door encyclopedia or vacuum-cleaner salesmen of yore. It's a profession that rewards stubbornness and persistence. (People absolutely hated telemarketing too, but it apparently was a successful sales channel.)
Check out Andrew's piece, and then see if you agree with my response. (You might also be interested in his little experiment in Usenet harvesting, The Spam Project.)
Posted by Brian at 7:35 PM | Comments (3)
Toxic-blog hype
Websense, which makes security software marketed to corporations, generated a lot of publicity this week with a warning about "toxic blogs."
The company says it discovered that crooks have created blogs designed to infect visitors with malicious software, including key-loggers and password stealers.
I'm not sure why this is a big story. Sure, it's a clever idea to plant malware in a seemingly safe public place.
But there's a key point missing from the Websense PR and most of the news coverage I've seen.
As an infection vector, a blog is ultimately like any other web page. To fall victim to Trojan horse software or "drive by" downloads implanted in a blog, you must be using a vulnerable web browser and be unprotected by anti-virus software.
In other words, if you're vulnerable to toxic blogs, you're probably already infected with malicious software.
Posted by Brian at 10:31 AM | Comments (1)
April 14, 2005
Phishers exploiting CapitalOne.com bug
![]() What's in your wallet? Phishing scam artists believe they can find out, thanks to a security bug at the Capital One web site.
What's in your wallet? Phishing scam artists believe they can find out, thanks to a security bug at the Capital One web site.
It's the latest version of an "open re-director" trick that's recently been used to exploit similar weaknesses at Ebay.com and ZDnet.com.
The sneaky technique works like this. A message arrives containing a hyperlink that appears to send recipients to the Capital One site so they can provide their account details. But the link actually uses a redirection feature at CapitalOne.com to whisk users off to a copycat phishing site.
Here's a phishing spam using the trick that showed up earlier this week on a mailing list for the Debian operating system.
For a harmless demonstration, click this URL and it will redirect you from the Capital One site to the FBI web site:
http://www.capitalone.com/redirect.html?dest=http://www.fbi.gov
CapitalOne even uses the re-director on its own login page. (Put your cursor on the orange "login" buttons and watch what URL appears in the browser status bar.)
As we've mentioned before, phishing scammers apparently hope the technique will serve two purposes. First, it will sneak their messages past URL blacklists. Second, it will "social engineer" spam recipients into thinking the message is actually from Capital One.
Posted by Brian at 9:49 AM | Comments (2)
April 13, 2005
"Rick Yang" sued by FTC and California
 The State of California and the FTC have teamed up to sue some California-based mortgage spammers.
The State of California and the FTC have teamed up to sue some California-based mortgage spammers.
The FTC said citizens forwarded 1.8 million spams that had originated from the defendants, Optin Global, Inc. (More evidence that the FTC reads its email after all!) The company is accused of massive CAN-SPAM violations.
Spamhaus lists "Calvin Ho" as the head of Optin Global, but that may have been an alias. The FTC complaint says Rick Yang is the owner and Peonie Pui Ting Chen serves as president.
Rick Yang?! That's the programmer who allegedly ripped off spam king Scott Richter a couple years ago!
Yang apparently was an expert in doctoring lists of email addresses so that they looked like the individuals had opted in to receive spam. His software would retroactively add IP addresses, date stamps, and other "proof" that the opt-in was legit.
Yang also apparently used the alias "gonka" and wasn't always prompt about paying his affiliates, according to this posting at SpamForum.biz.
Posted by Brian at 1:37 PM
"Bankrupt" Richter made $1.2M last year
Weep not for Spam King Scott Richter.
Sure, he's facing a $40M lawsuit from Microsoft that has driven his firm into bankruptcy. But, according to court records filed Monday and reviewed by the Denver Post, Richter paid himself a salary of over $1M in 2004.
Commenting on Richter's salary, father Steve told the Post: "Scott is obviously a very integral part of the company, and his compensation is commensurate with his contributions. It's in line with others in the industry."
Richter's company, OptinRealBig, grossed $19.6M last year. But its legal bills are mounting. According to the Post, the company spent over $500K on lawyers in just the first three months of 2005.
"Spamming is lucrative," concludes the Post article.
[Update: the Spamroll site has copies of the latest court filings available here and here.]
Posted by Brian at 9:30 AM | Comments (1)
April 11, 2005
Microsoft can't deal with Viagra spammer
 It's not easy keeping tabs on all the spam kings in the business. Spamhaus.org does an amazing job, but now and then another one pops up out of nowhere.
It's not easy keeping tabs on all the spam kings in the business. Spamhaus.org does an amazing job, but now and then another one pops up out of nowhere.
Case in point: George Merwyn.
According to this new article in the Boca Raton News, Merwyn is the (fake?) Viagra spammer Microsoft sued back in December 2003.
At the time, Microsoft didn't know Merwyn's name. It filed its lawsuit against WebMed-Rx.com, SafeMed-Rx.com, and 50 "John Doe" affiliates. Microsoft said the unidentified spammers spoofed Microsoft return addresses and used proxies to send the spam.
It took a while, but Microsoft finally tracked Merwyn down. Over a year later (Feb. 2005), Microsoft offered to drop the lawsuit for $100,000. But Merwyn refused, according to the Boca paper.
Merwyn reportedly lives in a $2.5 million house with wrought-iron gates and two guard dogs. Yet Spamhaus hasn't even heard of him.
How do you make that much scratch and yet stay off the Rokso list?
Even more perplexing, why not just pay the $100K and be done with it?
Perhaps it was the prospect of never being able to use Microsoft software again?
According to the article, Microsoft�s proposed settlement included "a permanent injunction that would have barred Merwyn and his roughly 50 accomplices, including his wife, from using Microsoft software including MSN internet access and MSN Hotmail."
[Update: Microsoft's anti-spam lawyer Aaron E. Kornblum informs me that the Boca Raton News goofed on this last aspect of the proposed settlement. According to Kornblum, Merwyn was simply barred from violating the terms of service of Microsoft's MSN or Hotmail services. There was no ban on using Microsoft products.]
Posted by Brian at 11:16 PM
Free Jeremy Jaynes!
 As you've no doubt heard, last week a Virginia judge upheld a November 2004 jury recommendation that spam king Jeremy Jaynes serve nine years for breaking that state's spam law. But in a new opinion piece for BetaNews, I argue that the sentence, which is under appeal, does not fit the crime and threatens to make a martyr of Jaynes.
As you've no doubt heard, last week a Virginia judge upheld a November 2004 jury recommendation that spam king Jeremy Jaynes serve nine years for breaking that state's spam law. But in a new opinion piece for BetaNews, I argue that the sentence, which is under appeal, does not fit the crime and threatens to make a martyr of Jaynes.
(P.S. For the sarcasm-impaired, I'm just kidding with that headline. Personally, I hope he enjoys his time with Bubba. I'm just predicting that the harsh sentence is going to backfire. I hope I'm wrong.)
Posted by Brian at 3:41 PM | Comments (2)
April 7, 2005
Safe from the spam flood?
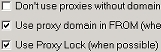 Remember the dire warnings earlier this year that a new feature in the Send-Safe spamware program might cause a flood of new spam?
Remember the dire warnings earlier this year that a new feature in the Send-Safe spamware program might cause a flood of new spam?
Well, turns out that Send-Safe's ProxyLock feature is seriously broken. As I detail in this new article for O'Reilly Network, CipherTrust researcher Dmitri Alperovitch has disassembled the latest version of Send-Safe, and he concludes that the dreaded ProxyLock f��������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������������s way: All this really brought home to me..." dc:creator="Brian" dc:date="2005-04-04T21:01:11-05:00" /> -->
April 4, 2005
Spam Kings on the spam blogs
 Two nice reviews of Spam Kings in recent days from my fellow spam bloggers.
Two nice reviews of Spam Kings in recent days from my fellow spam bloggers.
Most recently, Alan Rowe contributed a detailed review for the Spamfo site. Rowe concluded his review this way:
All this really brought home to me exactly what I thought was the main point of the book. That penis enlargement email winging its way towards you right now is and has been a subject of incredible passion -- from real people. I found Spam Kings to be a fascinating read and I thouroughly recommend it.
Besides reading Spam Kings, Rowe sought feedback from folks in the Nanae anti-spam newsgroup, which features prominently in the book. In the process, he discovered what he termed "a certain amount of conflict regarding McWilliams' book," especially surrounding the "heroine" of Spam Kings, an anti-spammer named Shiksaa.
![]() A few days ago, Michael Gracie, of the recently launched Spamroll blog, wrote up this generous appraisal of the book, a longer version of which was simultaneously published at the Slashdot.org "news for nerds" site.
A few days ago, Michael Gracie, of the recently launched Spamroll blog, wrote up this generous appraisal of the book, a longer version of which was simultaneously published at the Slashdot.org "news for nerds" site.
The Slashdot.org review of Spam Kings generated some interesting comments, including a couple heated ones from anti-spammers. I will respond to those remarks, and to the Shiksaa situation mentioned in the Spamfo review, in an entry here soon.
Posted by Brian at 9:01 PM
DotComBoiz in big trouble
The State of Florida is suing two Tampa spammers for $24M.
According to a complaint filed by the Florida Attorney general, Scott J. Filary, 25, and Donald E. Townsend, 34, ran an illegal spamming operation called DotComBoiz, Inc.
The two men allegedly sent illegal spams for drugs, cigarettes, "e-books," and copyrighted movies. (You can see their page soliciting affiliates who will send spam for them here.)
All the usual illegal spammer high jinks are alleged: forged headers, misleading subject lines, spoofing, etc. Plus some pretty serious allegations of fraud regarding their pharmacy sites, which filled prescriptions without being properly licensed or following safe dispensing procedures.
It wasn't mentioned in the complaint, but the DotComBoiz are already facing legal heat over their site downloaditall.com. The Motion Picture Associate of America reportedly sued them for helping Internet users find and download copyrighted movies.
Microsoft apparently helped track down the spammers, who allegedly sent thousands of spams to Microsoft "spam trap" accounts.
Posted by Brian at 11:53 AM
April 1, 2005
Butterfly attack on phishers
 Can trademark law bring phishing criminals to justice?
Can trademark law bring phishing criminals to justice?
That's what Microsoft is hoping with the 100-plus lawsuits it filed Thursday. Each lawsuit targets the (as-yet unidentified) operators of copycat sites designed to steal personal information from Microsoft customers.
According to court papers, the phishing perps misused Microsoft's trademarked butterfly logo and other marks to try to trick visitors into giving up their passwords, etc. The lawsuits also allege that the phishers violated federal computer fraud law.
The crooks created the look-alike sites using their own domains, such as PUNISH3R.NET, or by creating temporary sites at free web page services, such as one at http://newhotmail.4t.com/. (The phishing sites are no longer functional.)
These are all "John Doe" cases, meaning that Microsoft is hoping to use the discovery process to find out the true identities of the phishers. Microsoft's press release says the company "hopes to establish connections between phishing scams worldwide and uncover the largest-volume operators."
Best of luck to Microsoft. It usually takes many months of investigations and undercover operations for Federal law enforcement agencies to track down phishing scam artists.
But according to this recent Newsweek article, Microsoft's persistence paid off last year in a $3 million judgement against a 21-year-old Iowa phisher who worked at the local Blockbuster video store. I don't believe Microsoft has collected the money quite yet.
Posted by Brian at 5:00 PM | Comments (2)
