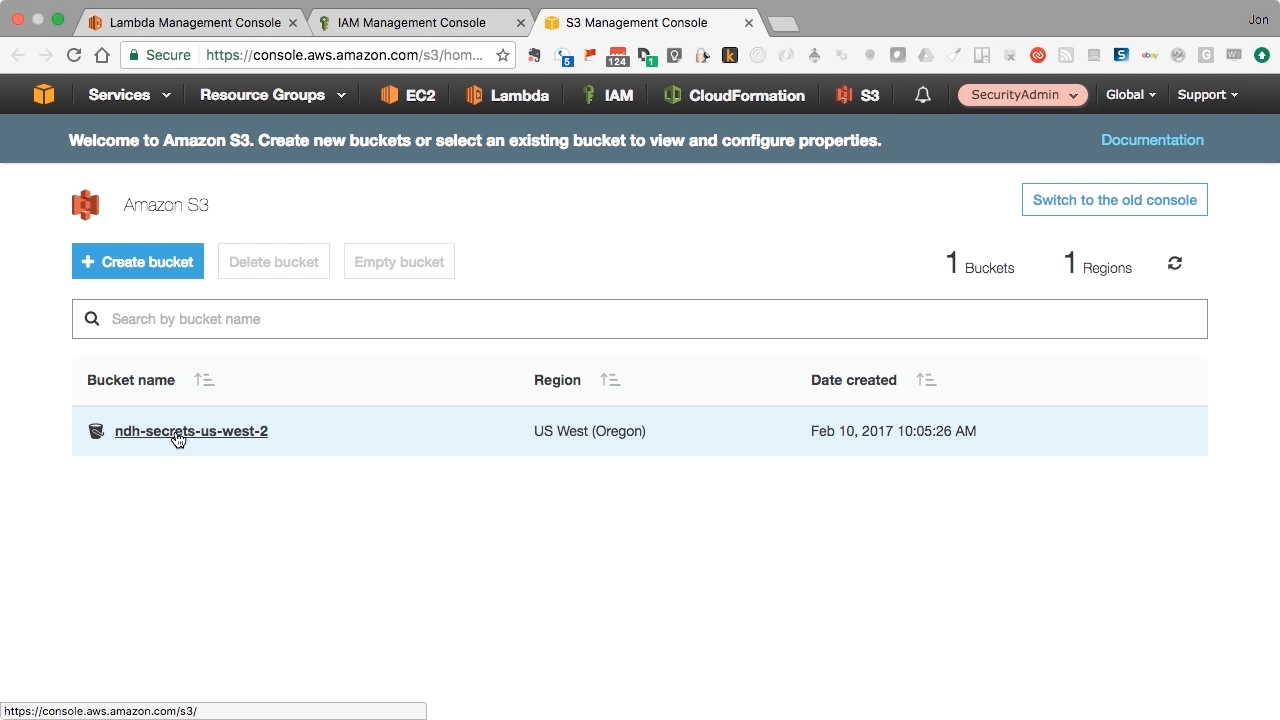
 Screen from "How can I retrieve application secrets securely with AWS Lambda? " (source: O'Reilly)
Screen from "How can I retrieve application secrets securely with AWS Lambda? " (source: O'Reilly) Transferring access credentials to your application in a secure fashion means separating “secrets” from source code. In this video Jon Gallagher explains how to go about uncoupling development from security using AWS Identity and Access Management users and roles. Database and application administrators and developers will learn how to to create audit logs of access to application secrets which may be needed to meet security compliance guidelines. Viewers should have prior knowledge of Boto3, Python, and access to AWS management console.
Access in-depth AWS training with our Build Apps for Amazon Web Services Learning Path.
Jon Gallagher has been working with public cloud computing for over 10 years, and is a certified instructor for both Amazon Web Services and Google Cloud Platform. Jon currently holds all five certificates for AWS and is a certified Google Cloud Engineer and a Google Certified Professional Architect. Jon has consulted for Fortune 500 companies and the US Military, as well as start-ups ranging from two-person operations to the newest unicorns. Jon has taught courses both in person across the U.S., and in virtual classrooms around world.