How can I scan my network using Nmap?
Learn how you can use Nmap to scan your network to find out which services and hosts are listening and may be vulnerable to compromise.
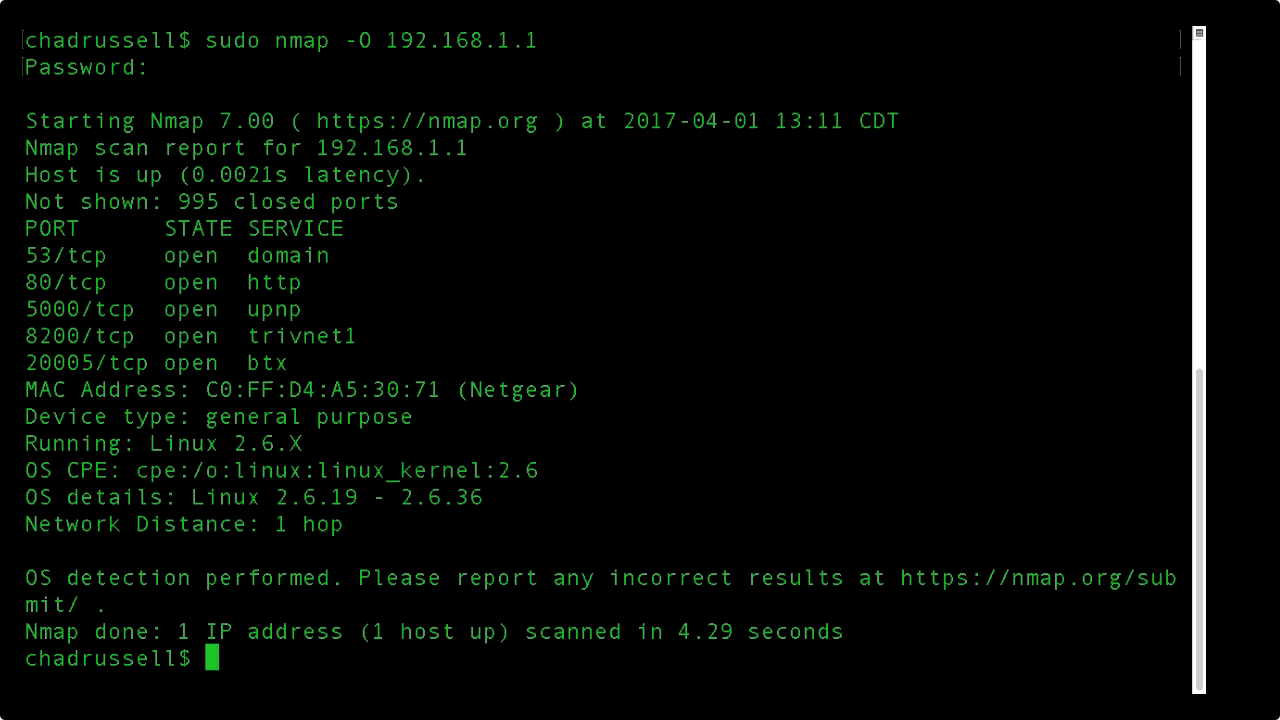 Screen from "How can I scan my network using Nmap?" (source: O'Reilly)
Screen from "How can I scan my network using Nmap?" (source: O'Reilly)
Scanning for vulnerabilities is the first step both when securing and when attacking a network. In this video, Chad Russell demonstrates how Nmap can be used to scan your network to find out which services and hosts are listening and may be vulnerable to compromise. All that is needed to follow along is access to a Linux operating system and a basic knowledge of the command line. System administrators and security engineers will be able to use this information proactively to patch and secure their networks before attackers exploit weaknesses.
Click here to increase your ethical hacking skills with more video training.
Chad Russell is a cyber security veteran of 15 years who has held CISSP, CCNP, MCSE, and MCDBA certifications. Chad has taught Microsoft Engineering courses as a certified trainer, and has acted as a security engineering consultant for companies such as SAP, Microsoft, and Oracle. Currently, Chad conducts security risk assessments for companies throughout North America with an emphasis on cloud security, identity governances, network security, social engineering, mobile security, breach assessments, database security, and access management.
