February 2018
Intermediate to advanced
396 pages
9h 38m
English
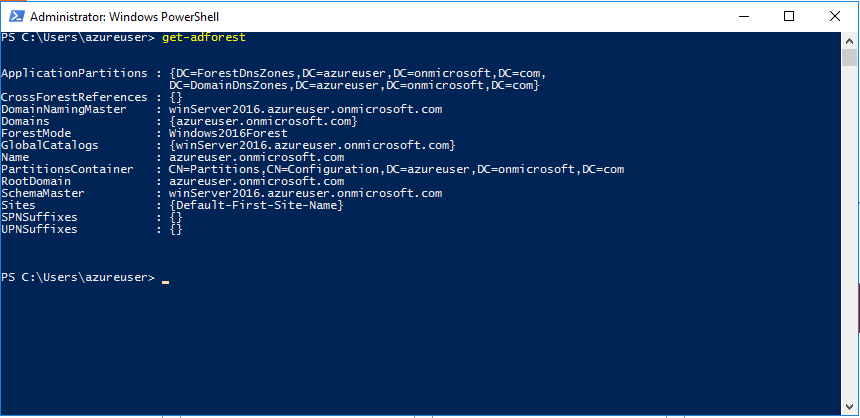
Kerberos is a high-profile target for attackers, as discussed in the previous section. But before diving deep into Kerberos attacks, let's discover some PowerShell capabilities.


Read now
Unlock full access