Actions on the intercepted requests
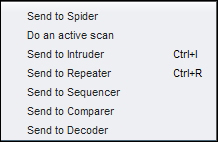
Once we have an intercepted request, we can send it to Repeater (Ctrl + R) to manipulate it one by one; we can send it to Intruder (Ctrl + I) to simulate an automated attack; we can send it for more spidering, an active scan or even to a Sequencer, Decoder, or Comparer (covered in the next chapter):
The question to ask is what should decide whether we should use Repeater or Intruder?. The short answer is, it is up to you. I personally use Repeater to figure out whether there is a flaw worth using Intruder or not. An active scan is always the last resort for the sake of completeness. This might change based on time ...
Get Burp Suite Essentials now with the O’Reilly learning platform.
O’Reilly members experience books, live events, courses curated by job role, and more from O’Reilly and nearly 200 top publishers.

