Chapter 10. Planning a Threat Control Strategy
This chapter covers the following topics:
• Trends in Information Security Threats
• Threat Control Design Guidelines
Integrated Threat Control Strategy
• Cisco Security Intelligence Operations
Threats
The time from knowledge of a vulnerability to the release of an exploit has decreased. Some exploits are designed to have global impact within minutes. Some exploits are also persistent and are difficult to eradicate.
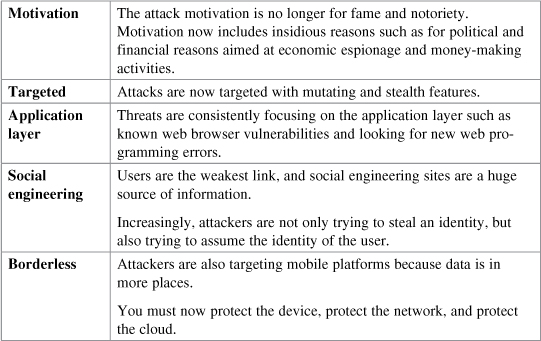
Trends in Information Security Threats
Threat Control Guidelines
General threat control guidelines include the following:
• Policies and processes must ...
Get CCNA Security (640-554) Portable Command Guide now with the O’Reilly learning platform.
O’Reilly members experience books, live events, courses curated by job role, and more from O’Reilly and nearly 200 top publishers.

