6.4. A Taxonomy of Cross-Layer Design Proposals
In the previous section, we took a quick look at the broad motivations for the different cross-layer design ideas in the literature. Having seen why the presence of wireless links motivates designers to violate layered architectures, we now turn our attention to how the layered architectures are violated in the different cross-layer design proposals.
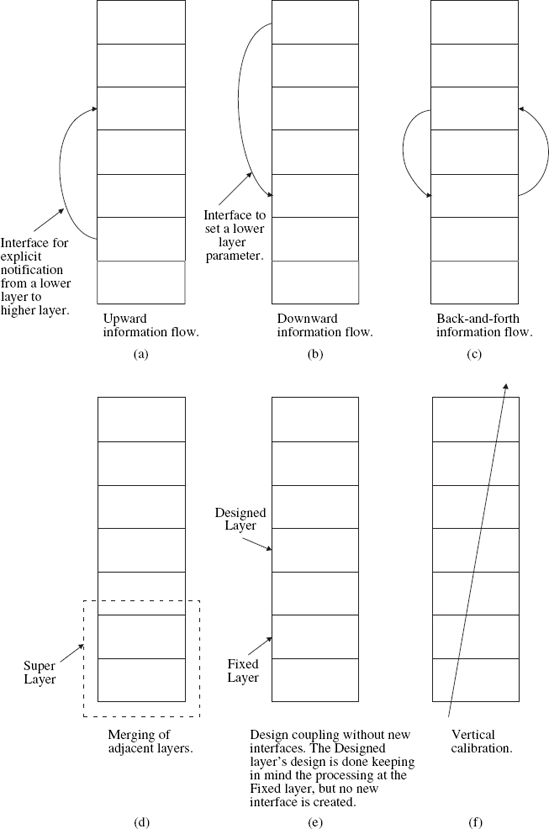
Based on the published research literature, we find that the layered architectures have been violated in the following basic ways:
Creation of new interfaces (Figure 6.1(a), (b), (c)).
Merging of adjacent layers (Figure 6.1(d)).
Design coupling without new interfaces (Figure 6.1(e)).
Vertical calibration across layers (Figure 6.1(f)).
We shall now discuss the aforementioned four categories in more detail and point out some relevant examples for the different categories. A few points are worth mentioning here. First, the examples that we point out are meant to be representative and not exhaustive. Secondly, the architectural violations that we identify can be combined to yield more complex cross-layer designs. Finally, the reference layered architecture we assume is a five-layer hybrid reference model that we discussed in Section 6.3.
Figure 6.1. Illustrating the different kinds of cross-layer design proposals. The rectangular boxes represent the protocol layers
6.4.1. Creation of New ...
Get Cognitive Networks: Towards Self-Aware Networks now with the O’Reilly learning platform.
O’Reilly members experience books, live events, courses curated by job role, and more from O’Reilly and nearly 200 top publishers.

