psscan is a useful plugin that allows the analyst to examine processes that have been terminated. As was previously discussed, pslist only shows the active processes. psscan can provide data as to the possibility of a rootkit through the examination of those processes that have been unlinked or hidden. The following command will execute the plugin:
forensics@ubuntu:~/Documents$ volatility -f stuxnet.vmem --profile=WinXPSP2x86 psscan
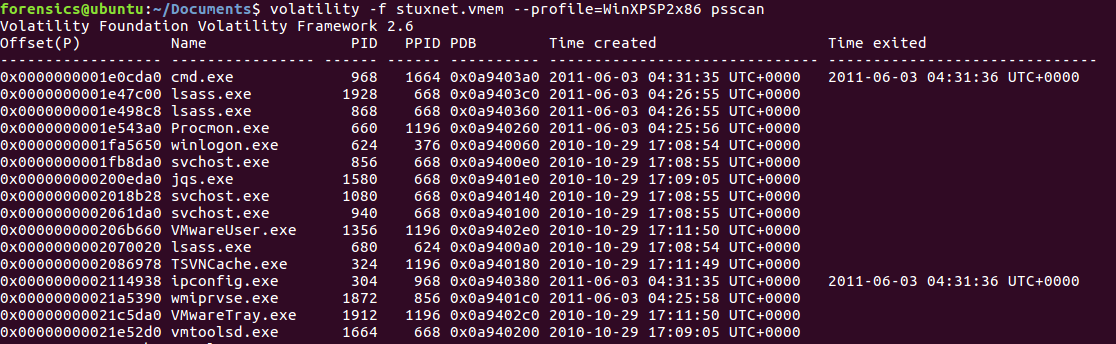
A review of the results indicates that neither of the suspicious processes have terminated. It is helpful though to have this output handy in the event that subsequent analysis reveals an associated process ...

