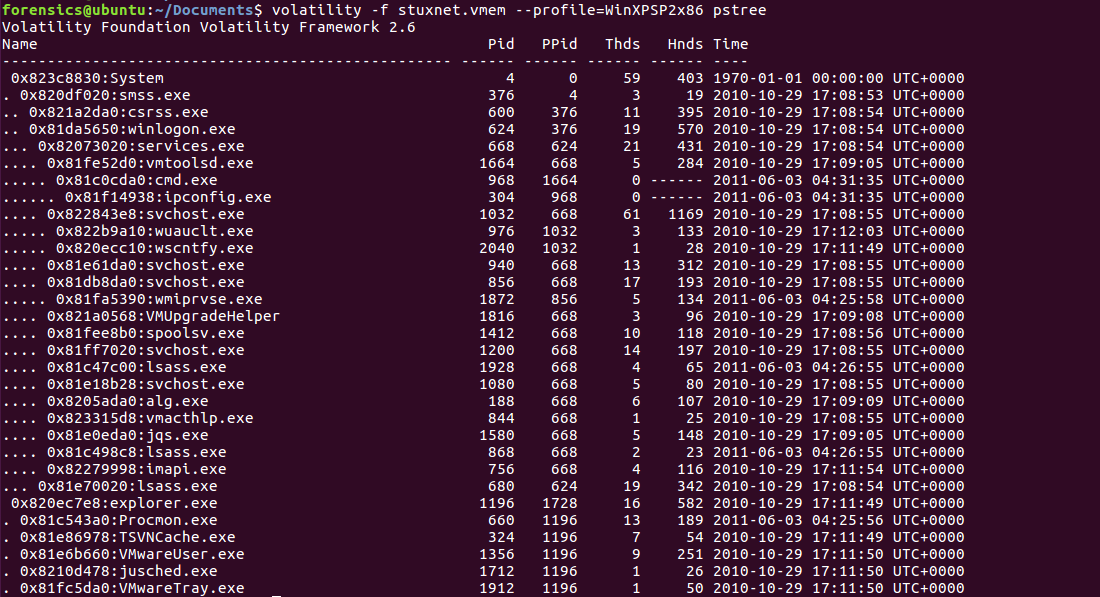
Often when examining system memory, it is necessary to have an understanding of what parent processes child processes are executed under. One indicator of a system being compromised is the identification of a process executed outside the normal parent process. The pstree plugin provides examiners a tree-like structure that identifies the parent process that is executing a potential suspect process. The Stuxnet image is run with this plugin, utilizing the following command:
forensics@ubuntu:~/Documents$ volatility -f stuxnet.vmem --profile=WinXPSP2x86 pstree
This produces the following output:
From an examination of these results, ...

