Two integrated tools that allow leveraging threat intelligence during an incident are Yara and Loki. Yara is often referred to as the Swiss Army Knife of pattern matching. It was created to assist malware researchers with classifying malware. Through the use of Boolean expressions and strings, a malware sample can be classified.
For example, the Yara rule (https://github.com/Yara-Rules/rules/blob/master/malware/APT_Cobalt.yar) for a variation of the Cobalt Strike looks like this:
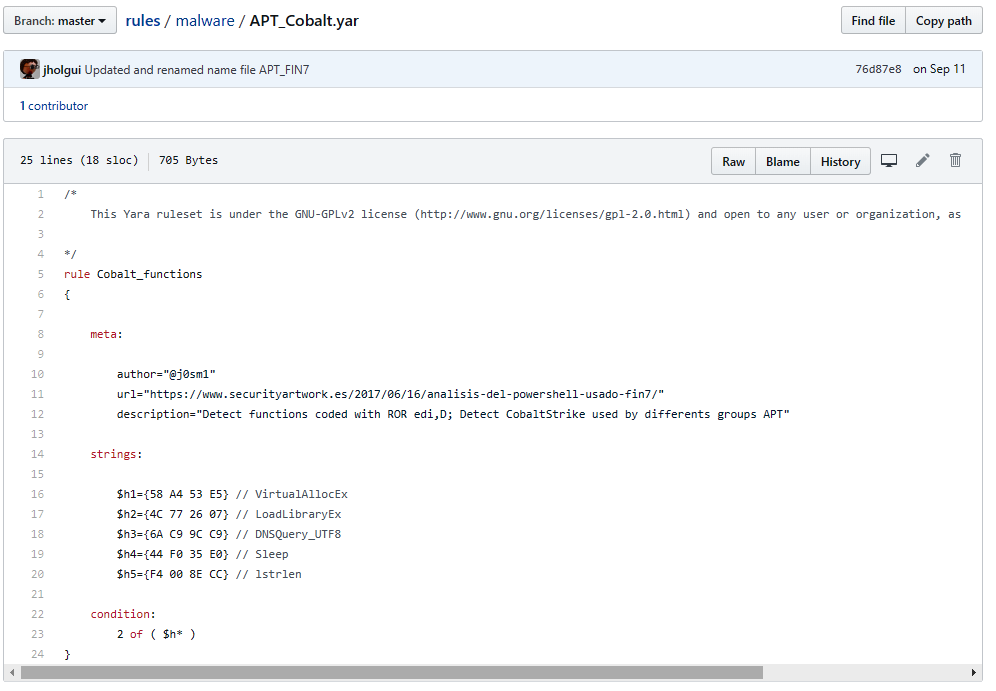
The preceding rule configures Yara to alert you to any strings found as Cobalt_functions.
Yara is available as a tool for use in malware research, but ...

