6.6.1 Transaction Security System
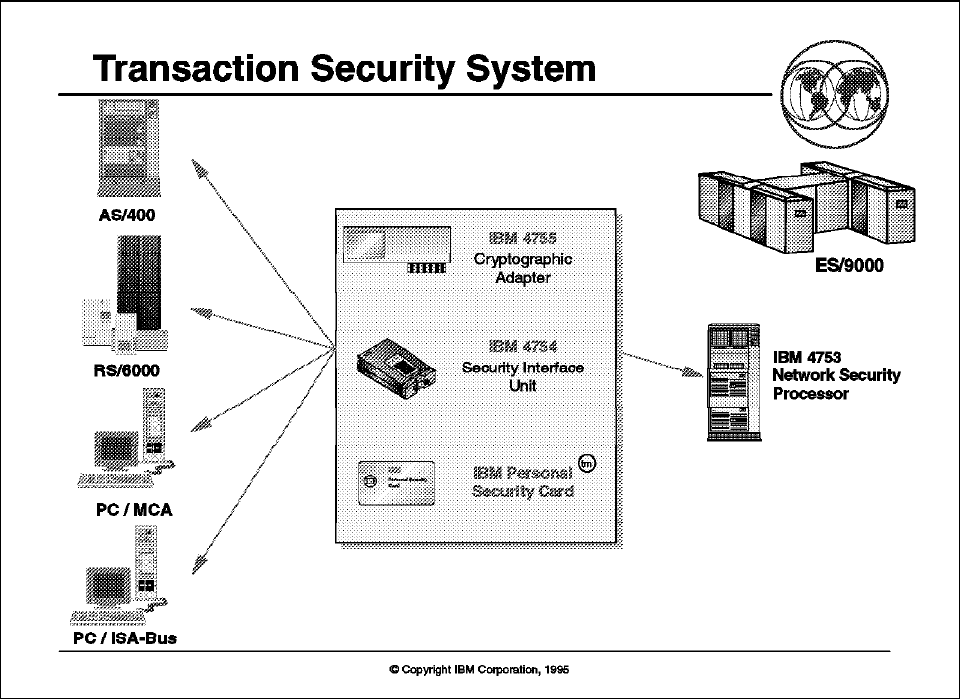
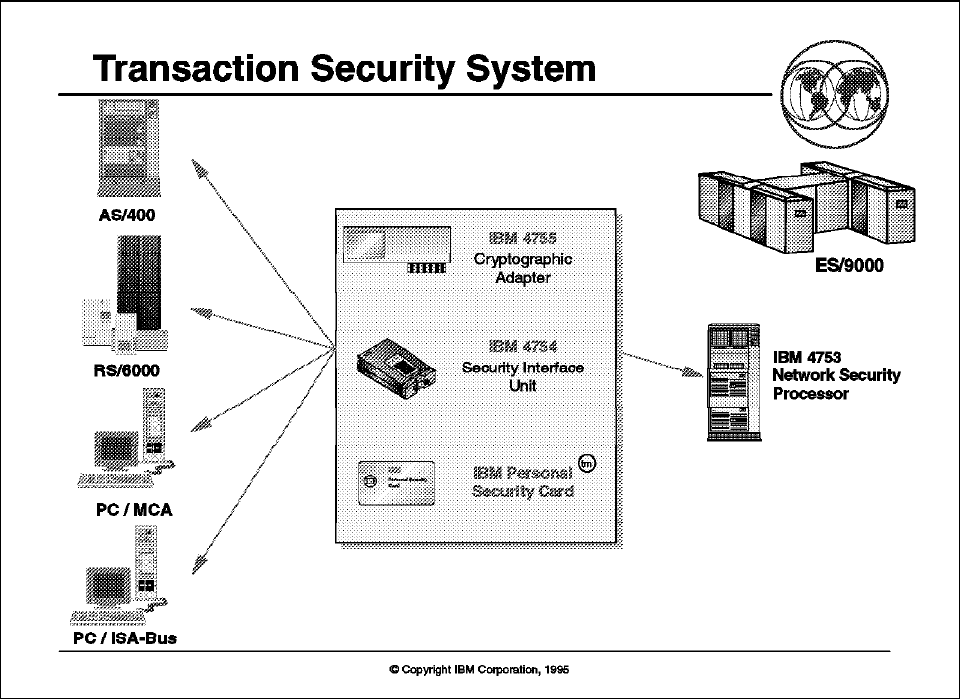
Figure 78. Transaction Security System
Key Points
The Transaction Security System provides a product family consisting of:
•
The IBM 4755 Cryptographic Adapter is available for the personal computer
(ISA-Bus, MCA-Bus) and RISC/6000 (MCA).
•
The IBM Personal Security Card is a credit-card sized “smart card” that
contains computer, memory and communication circuits in a single chip. DES
or CDMF is implemented on the Personal Security Card.
•
The IBM 4754 Security Interface Unit provides a Personal Security Card
reader and a 12 key keypad as an input/output device.
•
The IBM 2620 and 2628 Cryptographic Processors are AS/400 I/O ...