CHAPTER 13Recognizing Rogue URLs
Most phishing attempts include a rogue URL, which, if the potential victim clicks on it, will attempt to get the victim to perform an action against the victim's self-interests. The link may take the potential victim to a malicious website, attempt to launch malicious content, or ask the victim for confidential information. Teaching a user how to tell the difference between a legitimate and a rogue URL is one of the best skills that can be learned. Chapter 13 will cover how any user can tell the difference between a rogue and a legitimate URL link.
How to Read a URL
URL stands for uniform resource locator (URL), which is the formatting standard for representing the location of digital objects on networks. Simply, a URL is an address for an object on the Internet. The most common places people see URLs are in emails and the address location of their Internet browser. URLs most often represent objects and locations on the World Wide Web (WWW) but can point to objects using other protocols (e.g., File Transfer Protocol (FTP), Telnet, and 3270 terminals). Figure 13-1 shows an example of a common URL with its components identified.
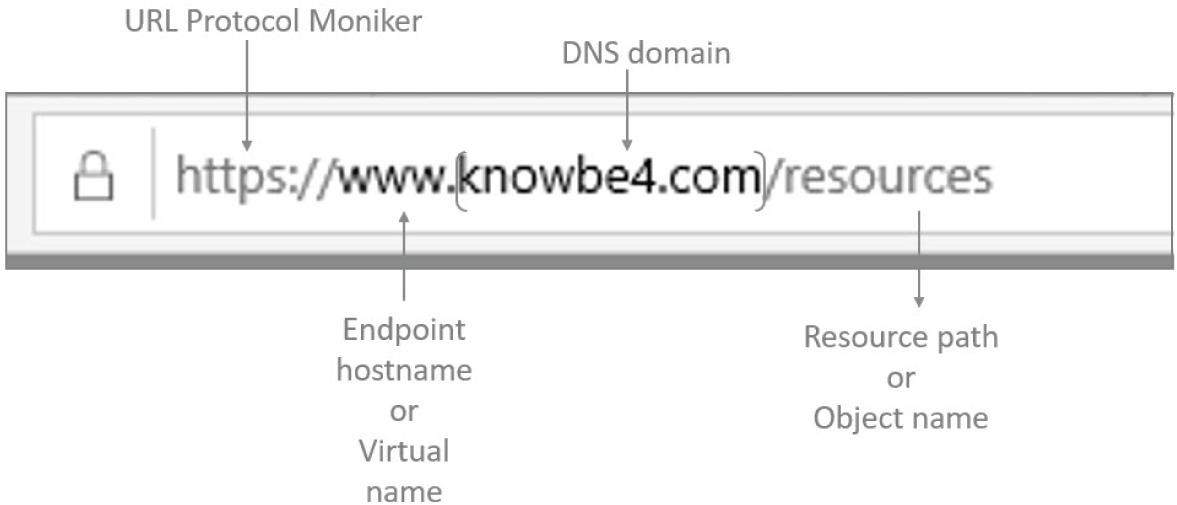
FIGURE 13-1 An example of a URL and its components.
Protocol Moniker
The beginning of URLs may include a moniker representing the protocol used to retrieve the object pointed to by the URL. Most people are used to ...
Become an O’Reilly member and get unlimited access to this title plus top books and audiobooks from O’Reilly and nearly 200 top publishers, thousands of courses curated by job role, 150+ live events each month,
and much more.
Read now
Unlock full access