Chapter 2
Payment Application Architecture
No fathers or mothers think their own children ugly; and this self-deceit is yet stronger with respect to the offspring of the mind.
—Miguel de Cervantes
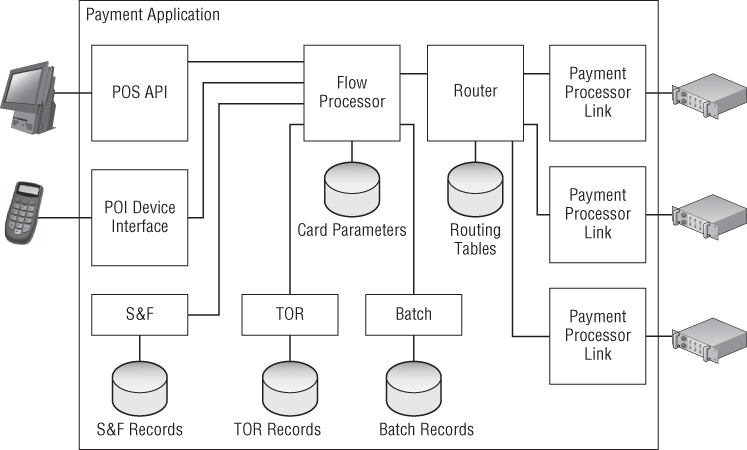
In order to understand all of the different types of threats that may break the payment application (PA), it is first necessary to learn about the internal structure of these systems. The details of concrete implementations may vary from vendor to vendor, but the main design principles remain closely similar due to the narrow specialization of such applications.
Essential Payment Application Blocks
Typical payment application architecture, shown in Figure 2.1, consists of external interfaces and processing modules. Interfaces are the bridges to the outer world. Processing modules drive the flow of the payment transaction.
Figure 2.1 Architecture blocks of a typical payment application
Interfaces
All systems need to communicate with the outside world of peripheral hardware and external software, so device and application interfaces are essential parts of any payment application. There are three types of external interfaces that connect the PA with devices and applications:
A single payment application may have several implemented interfaces of any type, depending on the required number of supported peripherals, POS models, ...
Get Hacking Point of Sale: Payment Application Secrets, Threats, and Solutions now with the O’Reilly learning platform.
O’Reilly members experience books, live events, courses curated by job role, and more from O’Reilly and nearly 200 top publishers.

