Take a look at the following code, which we wrote in order to carry out threat scoring on top of the MISP IOC collection. The whole code can be found at the following link: https://github.com/PacktPublishing/Hands-On-Penetration-Testing-with-Python:
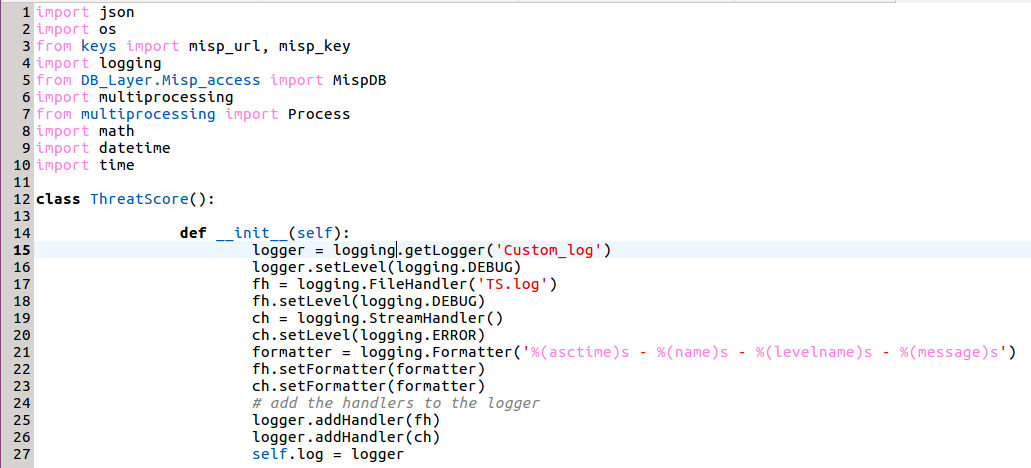
Let's try to understand the code written so far. This code makes use of the concepts we have studied earlier in this book. The idea is to read all the IOCs from the MISP attributes backend table and give a threat score to each, according to the logic discussed earlier. Now, there are millions of attributes, so if we try to read them and score them sequentially, it will ...

