Identity and Access Context
Most enterprise applications today need to have some form of security and permissions components in place to ensure that people who try to use the system are authentic users and are authorized to do what they attempt to do. As we just analyzed, a naive approach to application security builds users and permissions in with each discrete system, which creates a silo effect in every application.
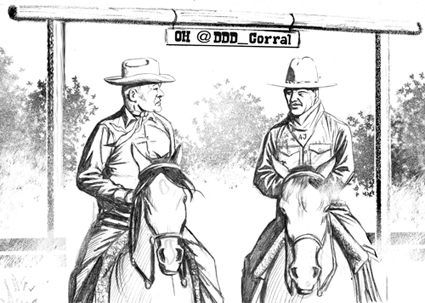
Cowboy Logic
LB: “You have no locks on your barns and silos, but nobody steals your corn?”
AJ: “My dog Tumbleweed cares for access management. It’s my own silo effect.”
LB: “I don’t think you really understand the book.”
The users ...
Get Implementing Domain-Driven Design now with the O’Reilly learning platform.
O’Reilly members experience books, live events, courses curated by job role, and more from O’Reilly and nearly 200 top publishers.

