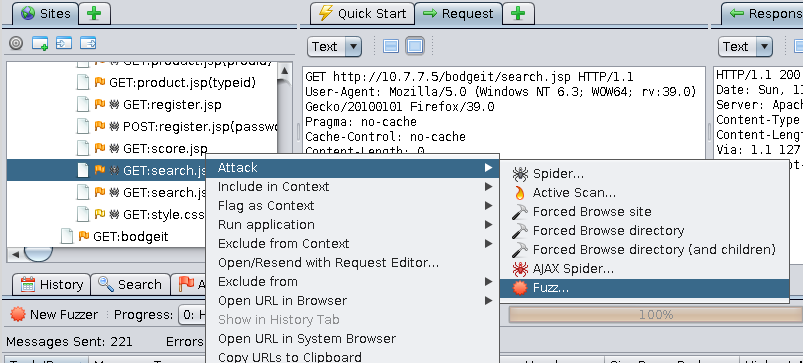
The OWASP-ZAP fuzzer can be run from the site map, the proxy's history, or the request panel by right-clicking on the request that you want to fuzz and selecting Attack | Fuzz..., as shown in the following screenshot:
After doing that, the fuzzing dialog appears where you can select the insert points; that is, the part of the request where you want to try different values in order to analyze server's responses. In the following example, we are selecting the q parameter's value in BodgeIt's search from the OWASP BWA vulnerable virtual machine:
Notice that two lists of payloads have already been added. To do that, ...

