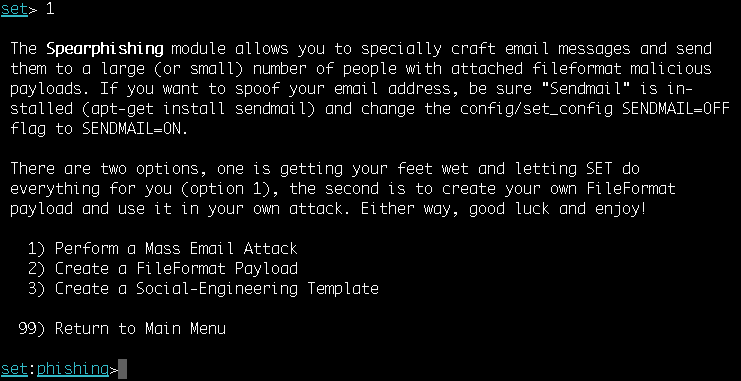
The spear-phishing module has three different attack vectors at our disposal:
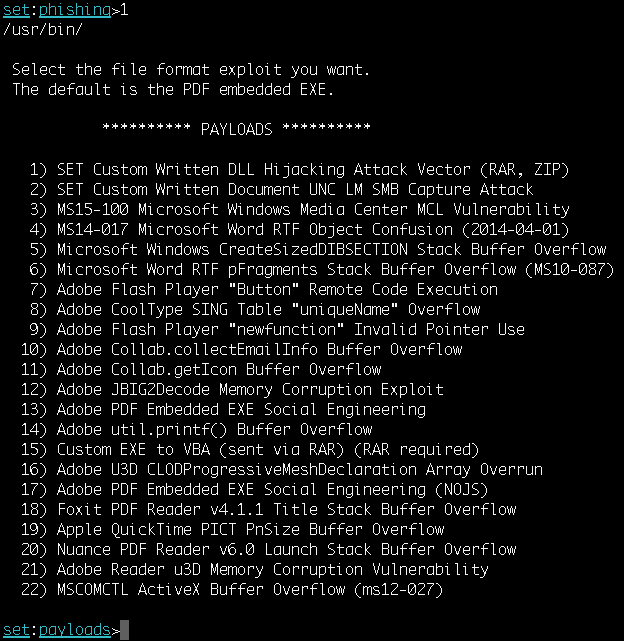
- Let's analyze first. Passing the first option will start the mass email attack. The attack vector starts by selecting a payload. You can select any vulnerability from the list of available Metasploit exploit modules:
- Then, we will be prompted to select a payload and specify the IP address or URL and the port for the listener.
- In the next few steps, we will be starting the sendmail server, setting a template for a malicious file format, and selecting ...

