In this attack, we'll use a similar setup to the credential-harvesting attack, this time embedding a custom Java applet into the page that prompts the user for execution privileges. Once the user accepts the prompt, the payload is executed and connects back to the our machine, allowing for remote access:
- Launch the Social Engineer's Toolkit again, enter 1 for Social Engineering Menu followed by 2 for Website Attack Vectors.
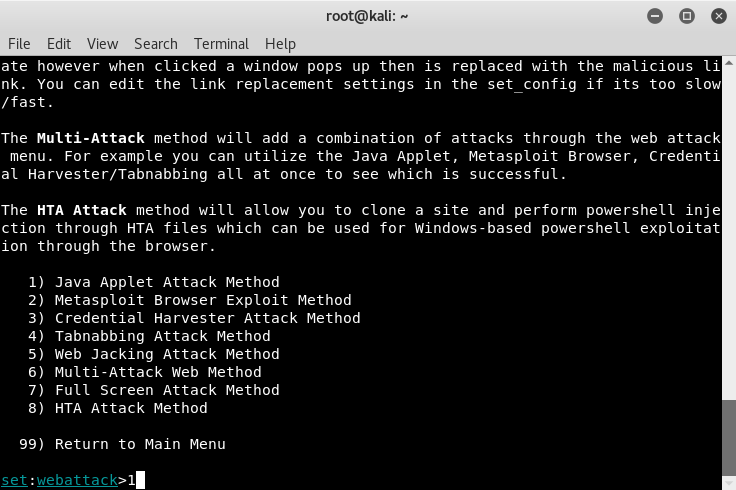
- From the menu, enter 1 for Java Applet Attack Method:
- Once loaded, we'll use the site cloner option from our previous example:
- You'll be asked whether you are using port-forwarding or NAT-enabled. ...

