We will now impersonate a real web site to gather credentials:
- From the Applications menu, select Social Engineering Tools | SET Social Engineering Toolkit. You will be presented with the following screen:
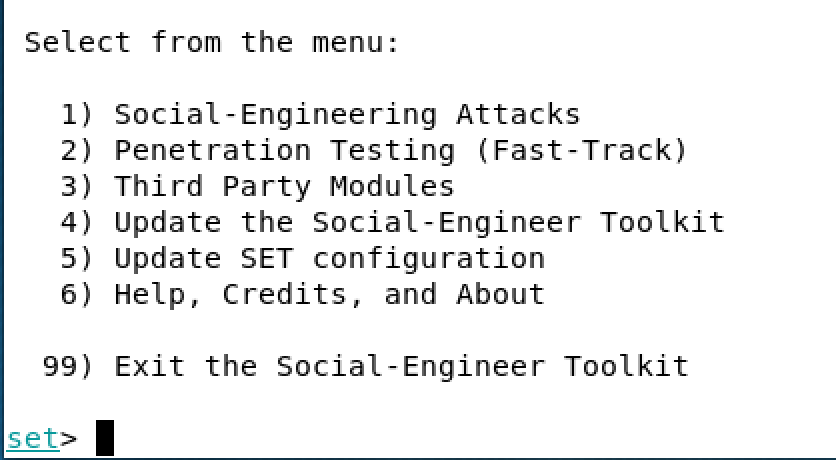
- Select the top option, 1) Social-Engineering Attacks.
- Select 2) Website Attack Vectors.
- Select 3) Credential Harvester Attack Method.
- Select 1) Templates.
- You will then be asked for the IP address of the post. Enter the IP address of Kali on the NAT network. You can open another terminal window and do ifconfig. I will enter 10.0.2.4:
- We will be given a list ...

