AP-less WPA-Personal cracking
In Chapter 4, we saw how to crack WPA/WPA2 PSK using aircrack-ng. The basic idea was to capture a four-way WPA handshake and then launch a dictionary attack.
The million dollar question is: Would it be possible to crack WPA-Personal with just the client? No access point!
Let's revisit the WPA cracking exercise to jog our memory:
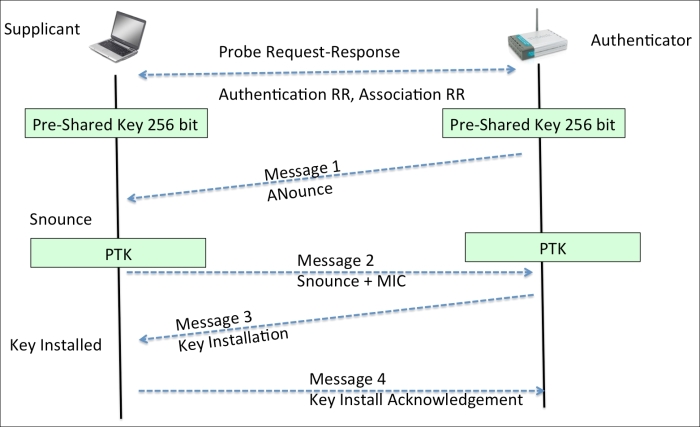
To crack WPA, we need the following four parameters from the four-way handshake—Authenticator Nounce, Supplicant Nounce, Authenticator MAC, and Supplicant MAC. Now, the interesting thing is that we do not need all of the four packets in the handshake to extract this information. We can get this ...
Get Kali Linux Wireless Penetration Testing : Beginner's Guide now with the O’Reilly learning platform.
O’Reilly members experience books, live events, courses curated by job role, and more from O’Reilly and nearly 200 top publishers.

