Identifying hidden files and directories with Python
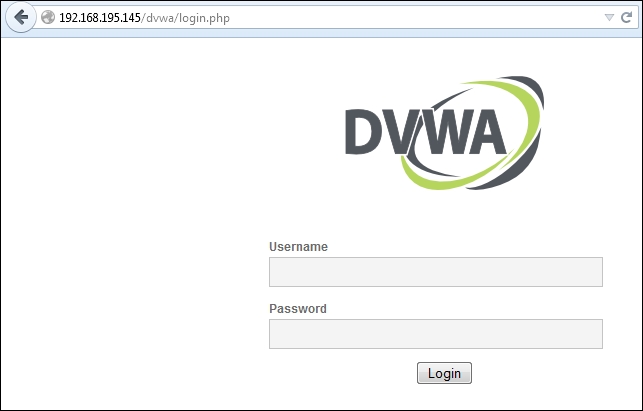
When we visit the site of the identified IP address, we see that it is the Damn Vulnerable Web Application (DVWA). We also see that it has appended the details of the default landing page to our initial request. This means that we start from the http://192.168.195.145/dvwa/login.php site as shown in the following screenshot:
We now have a starting location to test from, and using these details, we can look for hidden directories and files. Let's modify our last script to automatically look for hidden files or directories.
The best way to do this is to start within the base directory of the site ...
Get Learning Penetration Testing with Python now with the O’Reilly learning platform.
O’Reilly members experience books, live events, courses curated by job role, and more from O’Reilly and nearly 200 top publishers.

