Chapter 7. mTLS, Linkerd, and Certificates
Moving from a monolithic application to a microservices application puts us in a very interesting position as far as security is concerned. Where the monolith provided a natural security perimeter at the edge of its process, a microservices application has no natural security perimeter at all. Sensitive information that was previously protected by being passed in a function call inside the process now has to be sent over the network, as shown in Figure 7-1.
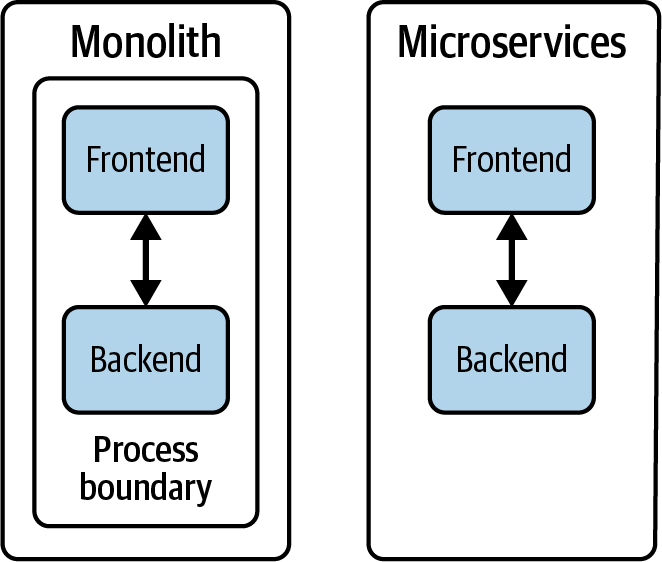
Figure 7-1. Security stance in a monolithic versus a microservices application
Additionally, the microservices are often running on infrastructure and network resources provided by outside teams, organizations, or even companies. If nothing is done to counter the threat, it’s all too easy for an attacker with access to the network to read, intercept, and modify communications between microservices. This is obviously a serious problem.
Finally, the network doesn’t even provide any secure way for a given microservice to know who made a call to it. The called microservice can find out the caller’s IP and MAC addresses, but these aren’t actually secure—it’s very easy to spoof the sender’s IP address, for example. Things just get worse when the application is running on a network it doesn’t control.
Secure Communications
To allow any microservices application to work, we need secure communications ...
Become an O’Reilly member and get unlimited access to this title plus top books and audiobooks from O’Reilly and nearly 200 top publishers, thousands of courses curated by job role, 150+ live events each month,
and much more.
Read now
Unlock full access