104 Chapter 4: Secure MPLS VPN Designs
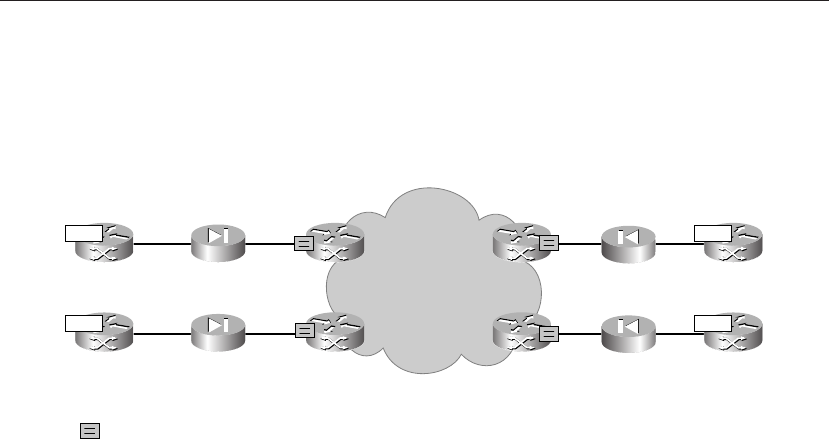
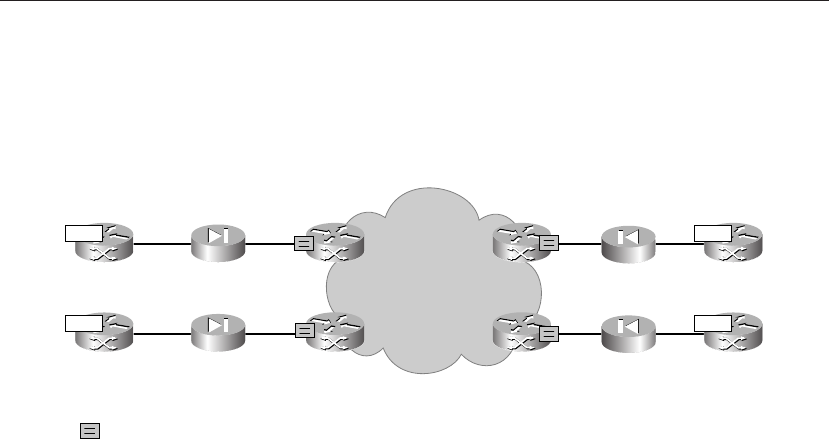
When different VPNs are connected in an extranet, or within one VPN site with different
security levels, firewalls should be positioned between the zones. Figure 4-15 shows an
example of how this can be achieved.
Figure 4-15 Firewalling Within a VPN or an Extranet
In this scenario, the firewalls are within the VPN they protect, and even the link between
the firewall and the PE router belongs to that VPN. Therefore, no virtualization is required
here, and normal enterprise firewalls can be used here.
It cannot be stressed enough that in all of these scenarios where routes are exchanged
through route-target configuration, ...