Chapter 4. Serialization
We’ve created a lot of classes thus far, including PrivateKey, S256Point, and Signature.
We now need to start thinking about how to transmit these objects to other computers on the network, or even to disk.
This is where serialization comes into play.
We want to communicate or store a S256Point or a Signature or a PrivateKey.
Ideally, we want to do this efficiently, for reasons we’ll see in Chapter 10.
Uncompressed SEC Format
We’ll start with the S256Point class, which is the public key class.
Recall that the public key in elliptic curve cryptography is really a coordinate in the form of (x,y).
How can we serialize this data?
It turns out there’s already a standard for serializing ECDSA public keys, called Standards for Efficient Cryptography (SEC)—and as the word “Efficient” in the name suggests, it has minimal overhead. There are two forms of SEC format that we need to be concerned with: uncompressed and compressed. We’ll begin with the former, and look at the compressed format in the next section.
Here is how the uncompressed SEC format for a given point P = (x,y) is generated:
-
Start with the prefix byte, which is
0x04. -
Next, append the x coordinate in 32 bytes as a big-endian integer.
-
Next, append the y coordinate in 32 bytes as a big-endian integer.
The uncompressed SEC format is shown in Figure 4-1.
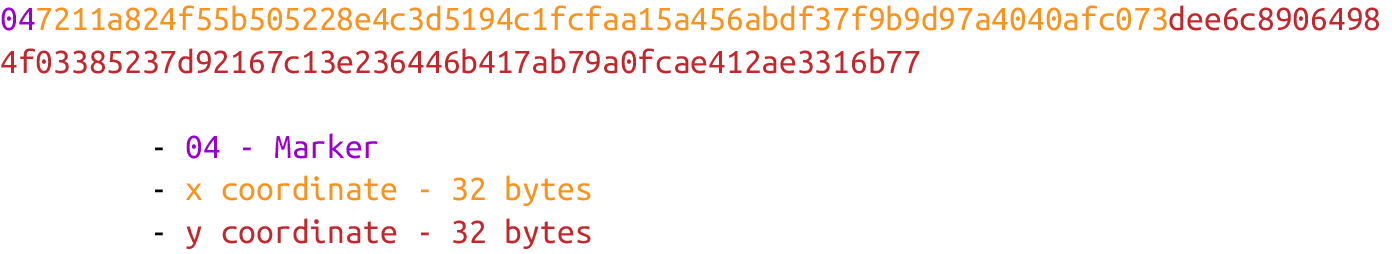
Figure 4-1. Uncompressed SEC format
Become an O’Reilly member and get unlimited access to this title plus top books and audiobooks from O’Reilly and nearly 200 top publishers, thousands of courses curated by job role, 150+ live events each month,
and much more.
Read now
Unlock full access