Appendix C: Security Control Assessment Requirements
This appendix provides supporting material for the chapters of the book. It can also serve as a reference source and illustrates how many security controls are allocated and the attributes of these controls in different situations and under different requirements.
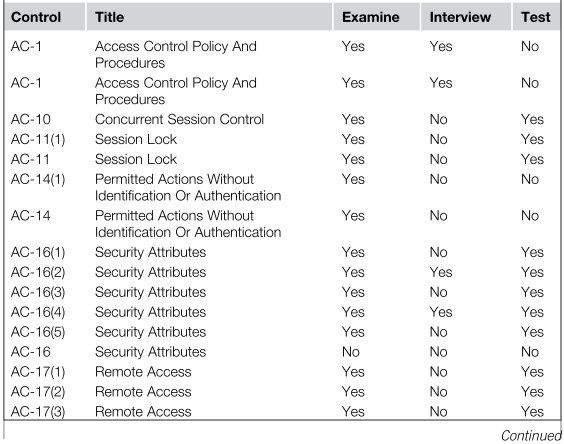
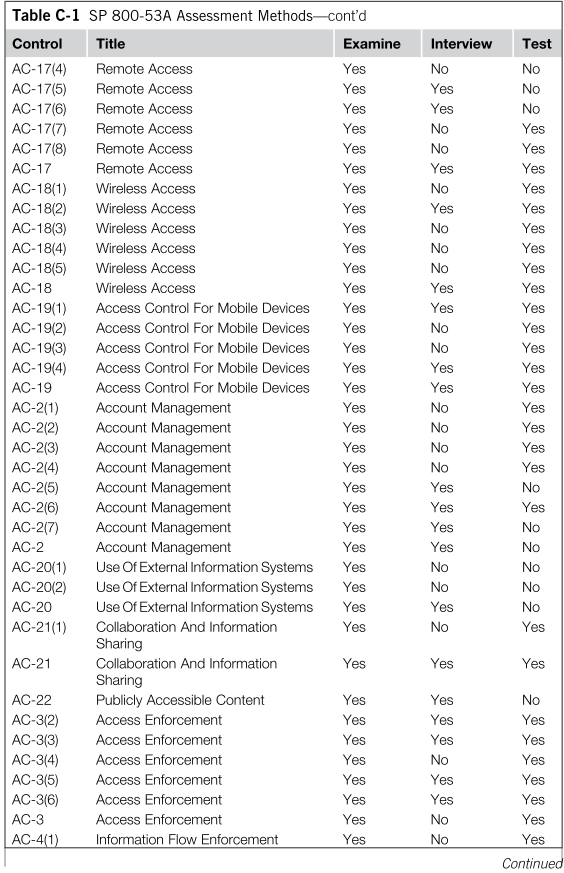
NIST SP 800-53A Assessment Methods
The following table defines the security assessment process used to evaluate each of the security controls as defined by NIST SP 800-53A.
Table C-1
SP 800-53A Assessment Methods
Get Risk Management Framework now with the O’Reilly learning platform.
O’Reilly members experience books, live events, courses curated by job role, and more from O’Reilly and nearly 200 top publishers.

