Chapter 6. Sensitive Data Exposure
The frequent news about data-breach incidents in recent years made it evident that sensitive information such as personal, financial, or health records is a lucrative target for attackers due to the associated monetary gains. A single data-breach incident could cause catastrophic losses for an organization. As published in a research study, Figure 6-1 shows the cost of data breaches in the year 2015 for 64 benchmarked companies, sorted by the number of breached records.
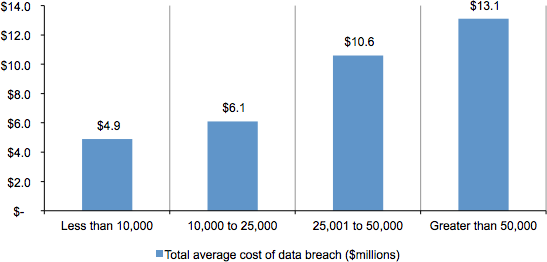
Figure 6-1. Total cost of data breach, based on monetary values and number of records stolen
Often, costs of sensitive data exposure span over incident investigation efforts, notifications to users, fines, lawsuits, settlements, as well as indirect costs such as loss of employee productivity, brand reputation, and user’s trust. In some cases, they result in businesses actually closing.
This Open Web Application Security Project (OWASP) risk primarily focuses on mitigating attacks that target web applications in an attempt to steal sensitive data. In this chapter, we go over related attack mechanics and ways to protect Node applications against it.
Attack Mechanics
There are three sources from which an attacker can steal the sensitive data managed by applications: a client such as a browser, a network, or application servers. Let’s review each.
Stealing Sensitive Data from a ...
Become an O’Reilly member and get unlimited access to this title plus top books and audiobooks from O’Reilly and nearly 200 top publishers, thousands of courses curated by job role, 150+ live events each month,
and much more.
Read now
Unlock full access