Examples of rogue unsolicited email messages
Figures A.4 and A.5 show examples of rogue unsolicited email messages.
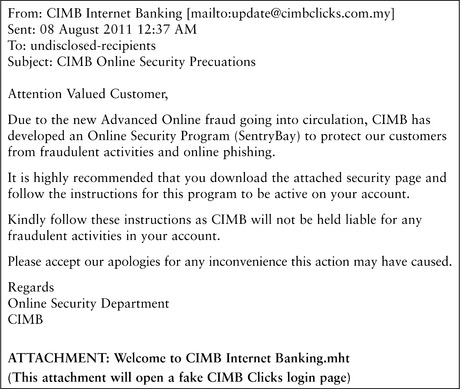
Figure A.4 Message sent by email purporting to come from CIMB Internet Banking, example 1 Source: CIMB Bank and CIMB Islamic [2011]
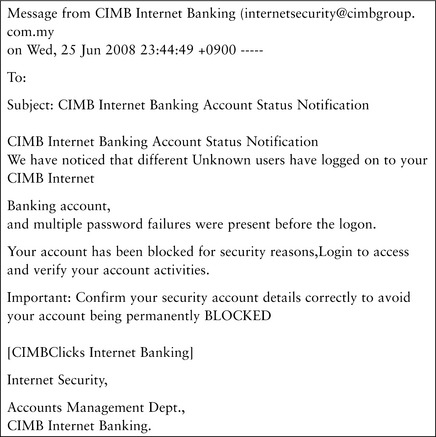
Figure A.5 Message sent by email purporting to come from CIMB Internet Banking, example 2 Source: CIMB Bank and CIMB Islamic [2008]
Get Security Risks in Social Media Technologies now with the O’Reilly learning platform.
O’Reilly members experience books, live events, courses curated by job role, and more from O’Reilly and nearly 200 top publishers.

