Chapter 16. Electronic Mail and News
From a user’s point of view, electronic mail is one of the most crucial Internet services. Mail, along with news, provides a way for people to hold discussions with other people, singly or in groups. This chapter discusses the security issues related to electronic mail and news protocols, including SMTP, POP, IMAP, MIME, and NNTP.
Electronic Mail
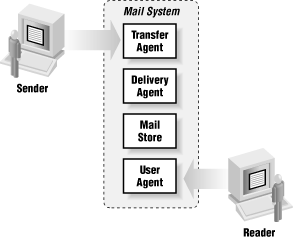
Traditionally, a mail system has three parts, which may be implemented by different programs or by the same program, in any combination:
- Mail transfer agent (MTA)
Accepts mail from external hosts or sends it to external hosts
- Mail delivery agent (MDA)
Puts the mail in the correct mailbox on the local host
- Mail user agent (MUA)
Lets the recipient read the mail and compose outgoing mail
Figure 16.1 shows a large mail system and its parts.
 |
Each of these parts is vulnerable for a different reason:
The transfer agent directly accepts commands (related to transporting mail) from external hosts; for this reason, if the transfer agent isn’t secure, it may end up immediately giving an attacker all the access it has itself.
The delivery agent needs special permissions because it needs to be able to write into every user’s mailbox. Although the delivery agent doesn’t need to talk to the external world, if it can be subverted somehow, the intruder obtains very broad access.
The user agent ...
Get Building Internet Firewalls, 2nd Edition now with the O’Reilly learning platform.
O’Reilly members experience books, live events, courses curated by job role, and more from O’Reilly and nearly 200 top publishers.

