Understanding Mobile Devices
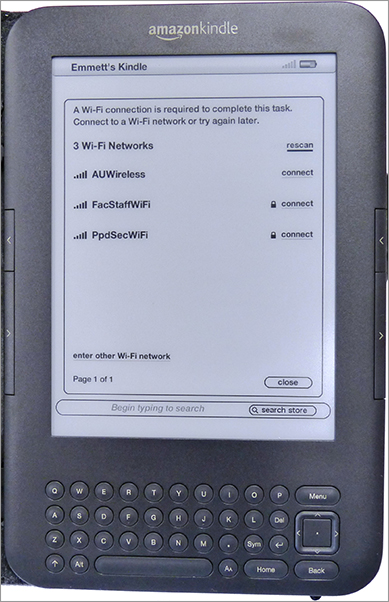
Mobile devices, including smartphones, e-readers, tablet computers, and personal digital assistants (PDAs), are popular. Many of these devices use either RF signaling or cellular technologies for communication. Figure 12-5, for example, shows an Amazon Kindle looking for wireless networks.
Figure 12-5: Wireless scanning is done by a wide variety of devices such as the Kindle.
If the device uses the Wireless Application Protocol (WAP), the device in all likelihood doesn’t have security enabled. Several levels of security exist in WAP:
Anonymous Authentication This allows virtually anyone to connect to the wireless ...
Get CompTIA® Security+™: Study Guide, Fifth Edition now with the O’Reilly learning platform.
O’Reilly members experience books, live events, courses curated by job role, and more from O’Reilly and nearly 200 top publishers.

