Renegade
For all three browsers, we’ll use
the same applet, called Renegade.
Renegade isn’t really dangerous, but it does
try to find out your name, using
System.getProperty("user.name").
This action is not allowed in the applet sandbox, to protect the
privacy of the user. In Renegade, we enclose this
call in a try block in case a
SecurityException is thrown. Save the source code for this class in
Renegade.java.
import java.applet.*;
import java.awt.*;
public class Renegade extends Applet {
private String mMessage;
public void init() {
try {
mMessage = "Your name is " + System.getProperty("user.name") + ".";
}
catch (SecurityException e) {
mMessage = "Can't get your name, due to a SecurityException.";
}
}
public void paint(Graphics g) {
g.drawString("Renegade", 25, 25);
g.drawString(mMessage, 25, 50);
}
}The HTML page that contains this applet, Renegade.html, is as follows:
<html> <head> </head> <body> <applet code = Renegade width = 300 height = 200></applet> </body> </html>
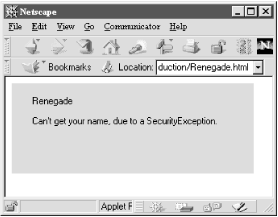
If you point your browser at this applet, the call to
System.getProperty() fails, just as we expected.
Figure 8.1 shows this applet in Navigator 4.01.
 |
Get Java Cryptography now with the O’Reilly learning platform.
O’Reilly members experience books, live events, courses curated by job role, and more from O’Reilly and nearly 200 top publishers.

