Combining Services
When combining multiple services, the general path must be remembered in the forward and reverse directions (see Figure 8-11). This is especially true when NAT is deployed to determine whether the pre- or post-NAT address should be used to match a rule. In the forward path from a LAN interface to a WAN interface, IDS and stateful firewall are performed first, then NAT, and finally IPSec. This means that the stateful firewall must match on a pre-NAT address whereas the IPSec tunnel would match on the post-NAT address.
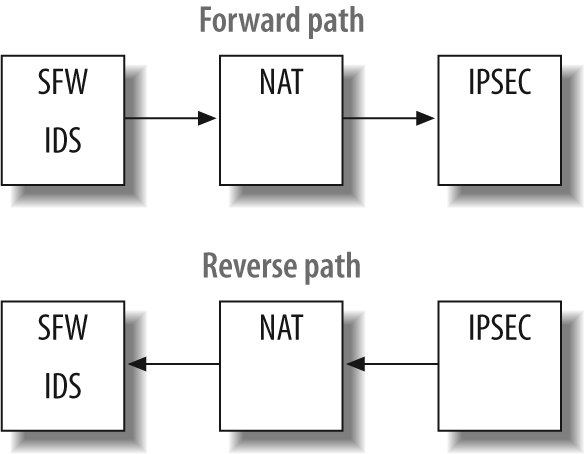
Figure 8-11. Service path
In the return path, the IPSec packet will be processed first, then NAT, and finally the stateful firewall. This still allows IPSec to match a public address and the stateful firewall to match on a private address.
Everything becomes much more complicated when IPSec over GRE is implemented in the router with other services turned on. This is because JUNOS treats GRE packets in a very peculiar fashion after GRE encapsulation. After a packet is encapsulated in a GRE packet, it is marked with an input interface as the next hop outgoing interface. This causes GRE packets to be blocked if any input filters or input services are allowed that do not allow for this service.
In Figure 8-12, an IP packet comes into the fe-1/0/0.42 interface and a route lookup is performed that directs the packet into a GRE tunnel, which has an egress interface ...
Get JUNOS Enterprise Routing now with the O’Reilly learning platform.
O’Reilly members experience books, live events, courses curated by job role, and more from O’Reilly and nearly 200 top publishers.

