Dynamic DNS is Windows 2000 and Windows Server 2003’s way of bringing together the one good feature of WINS—automatic machine registration and record updating—with the resiliency and open standards advantage of DNS, a staple of the Internet. With dynamic DNS, machines running Windows 2000, Windows XP, or Windows Server 2003 will register their presence automatically with the nameserver that controls the zone associated with their connection’s DNS suffix. In the case of the examples so far in this chapter, if I have a machine named sales1.north.mycompany.com, Windows automatically would register an A record for that hostname and IP address with the nameserver that controls north.mycompany.com—a handy feature, indeed.
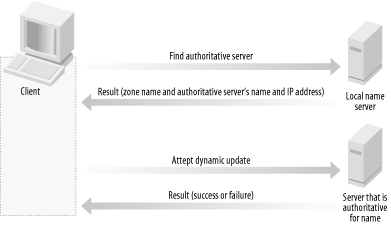
Figure 4-16 shows the actual flow of dynamic DNS registration when a workstation needs to register itself.
The process works a bit different when IP addresses are assigned by a Windows DHCP server. The client, when it receives its IP address from the DHCP server, only registers an A record in the nameserver’s forward lookup zone. The DHCP server by default is responsible for registering the PTR records in the nameserver’s reverse lookup zone, if one exists.
Tip
If you want to alter this behavior, you can configure the DHCP server to take care of both parts of the registration by looking on the properties sheet for the DHCP scope in question within the DHCP snap-in.
Open the DHCP snap-in, expand your machine in the left pane, and then click Scopes. In the right pane, select the scope you want to alter and then right-click it and select Properties. Now, navigate to the DNS tab and select Always Update DNS. The DHCP server will register A records in the forward lookup zone and PTR records in the reverse lookup zone for all clients leasing an address.
When does this registration take place? Five actions will trigger a DNS registration on the part of the client:
The computer has been restarted.
The computer’s DHCP lease, if the machine uses a dynamic IP address, has just been renewed.
The computer’s statically assigned IP address has been changed.
A full 24 hours have passed since the last DNS registration on record.
An administrator issues the
ipconfig /registerdnscommand from the command-line.
Tip
Although the default period for reregistering DNS dynamically is 24
hours, you can change this value inside the Registry. On the
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\Tcpip\Parameters
key, add a new REG_DWORD entry called
DefaultRegistrationRefreshInterval, and give it a
value in seconds. (For reference, there are 86,400 seconds in a day.)
Obviously, with multiple machines registering DNS information periodically throughout the day, you need to clean up that information when it expires. The Windows Server 2003 DNS scavenging process finds the dynamically registered records that haven’t been updated for some time, and then simply deletes them to ensure that after a delay for propagation between servers, the zone information contains the most up-to-date data on the machines and addresses therein.
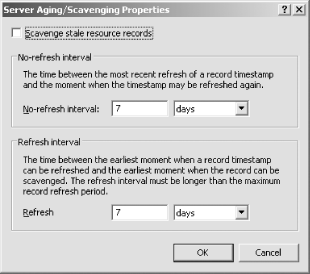
Let’s take a look at how scavenging is presented in the user interface and how you can best control it. To control scavenging for all zones on a particular nameserver, inside the DNS Management snap-in right-click the server’s name and select Set Aging/Scavenging for All Zones. The Server Aging/Scavenging Properties screen appears, as shown in Figure 4-17.
At the top of the screen, you see the master switch to enable scavenging. Additionally, you see two options. One of them is for the no-refresh interval, which simply is the time a dynamically registered record should be allowed to stay registered in a “read-only” fashion before the scavenger can take a look at it. This means client computers cannot reregister themselves during this period. The other option is for the refresh interval, which is the amount of time a record should remain and be allowed to be refreshed after the no-refresh interval has passed before the scavenger should remove it. In essence, the scavenger process is not allowed to touch a record unless both the no-refresh and the refresh intervals have passed in full.
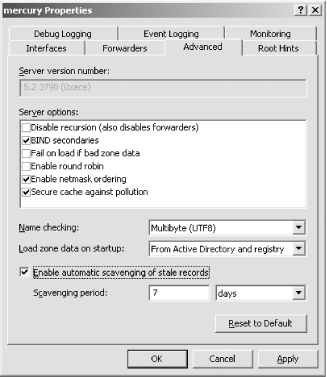
To enable scavenging, check the top checkbox and click OK. If you have Active Directory-integrated zones, you’ll be asked to confirm your choice for those as well. Click OK once again, and scavenging will be enabled. Another step remains—you need to enable scavenging on the nameserver, which you can do by right-clicking the server name inside DNS Management, selecting Properties, and clicking the Advanced tab. This is shown in Figure 4-18.
At the bottom of the screen, check the checkbox labeled Enable automatic scavenging of stale records, and then enter a period of time after which the scavenger can automatically engage.
If you want to control scavenging and its associated intervals for an individual zone, right-click the zone inside DNS Management and select Properties. Then, navigate to the General tab and click the Aging button. The screen is identical to the server-wide scavenging control screen shown in Figure 4-17.
For the scavenging service to do the mathematics required to calculate these intervals, the DNS service adds a nonstandard bit of information to a resource record’s zone information. For instance, an A record on a server or zone with scavenging enabled might look like this:
colossus [AGE:47363030] 36400 192.168.0.5
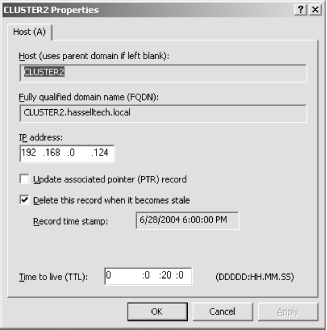
The AGE portion is the inception point of the record, measured in some small interval since a certain date. That really doesn’t matter; the concept is that with scavenging enabled, the AGE information is added to a DNS record so that the no-refresh and refresh intervals can be honored correctly. You can see that timestamp in a human-readable format by right-clicking any record in the DNS Management snap-in and selecting Properties. The Record timestamp field will show the date and time the record was created in DNS, as shown in Figure 4-19.
If your organization hasn’t deployed Active Directory yet, the dynamic DNS registration default settings that modern Windows client operating systems have can be aggravating to IT groups—your nameservers will be pelted, sometimes forcefully, with registration attempts from Windows systems that believe that for an Active Directory in your organization, they need to register themselves. Of course, that’s not necessarily true, but it’s the default behavior.
Fortunately, you can turn this off, either through a registry change (to make the modification on a larger scale) or through the GUI. To do so through the GUI, follow these steps:
Open the connection’s properties.
On the Network tab, select TCP/IP, and then click the Properties button.
Navigate to the DNS tab.
Uncheck Register this connection’s addresses in DNS.
Click OK.
To do so through the Registry, open the Registry Editor, and then take the following steps:
Navigate through
HKEY_LOCAL_MACHINE\CurrentControlSet\Services\TcpIp.Click the Parameters key.
Add a new value, of type
REG_DWORD, calledDisableDynamicUpdate.Set the value of the new entry to 1.
Alternatively, you can type the following at the command-line:
reg add hklm\system\currentcontrolset\services\tcpip\parameters /v DisableDynamicUpdate /t REG_DWORD /d 1 /f
You also can use Group Policy (GP) to deploy a policy that disables this to all machines in a domain, or to a subset of those machines, but GP in this case necessitates Active Directory. In any case, the proper object is under Computer Configuration/Administrative Templates/Network/DNS client. The object is called Dynamic Update, and to turn it off, change the state to Disabled. Chapter 6 covers GP in more detail.
Get Learning Windows Server 2003 now with the O’Reilly learning platform.
O’Reilly members experience books, live events, courses curated by job role, and more from O’Reilly and nearly 200 top publishers.