Design Rationale
In Chapter 9, it was discussed how it was essential for LTE/SAE to separate the communication between the core and the UE to the AS and the NAS. This separation was also applied in terms of security whereby the security of the AS (i.e., RRC security in eNB) was separated from the security of the NAS signaling. Two other relevant decisions were made in the design of the security architecture for LTE. The first is that the user plane security terminates above the eNB; the second, that the radio link and the core network must have cryptographically separate keys. These requirements result in LTE having two layers of protection, differentiating the E-UTRAN from the UTRAN which only a one layer perimeter security. These two layers are shown in Figure 14.1, where the first provides the RRC security and the User plane protection, while the second layer provides the NAS signaling security.
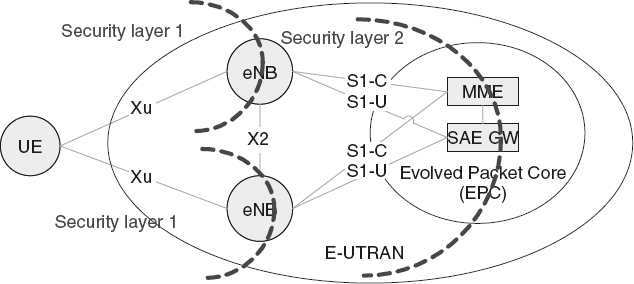
Figure 14.1 First and second security layers in LTE. Reproduced by permission of © 2010 3GPP. Further use is strictly prohibited.
The immediate advantage of this rationale is that a compromise at the first layer (i.e., if an eNB or an HeNB is compromised), it would be hard to compromise the security of the eNB/HeNBs (i.e., other elements in the first layer) or the core (i.e., layer 2). This means that placing eNBs in vulnerable locations is more practically accessible in LTE.
Resources ...
Get LTE, LTE-Advanced and WiMAX: Towards IMT-Advanced Networks now with the O’Reilly learning platform.
O’Reilly members experience books, live events, courses curated by job role, and more from O’Reilly and nearly 200 top publishers.

