Chapter 7. Assessing Web Applications
This chapter details assessment of web applications found running on web servers. A number of technologies and platforms are used by organizations to run and support web applications, including Microsoft ASP.NET, Sun JSP, and PHP. Upon performing web server assessment and crawling to identify web application components and variables, we can perform deep manual web application testing to compromise backend server components through command injection and other attacks.
Web Application Technologies Overview
Web applications are built and delivered using technologies and protocols across three layers:
Presentation tier
Application tier
Data tier
Figure 7-1 (as prepared by the OWASP team) shows these layers and associated web browser, web server, application server, and database technologies, along with the protocols that allow data to be exchanged between tiers.
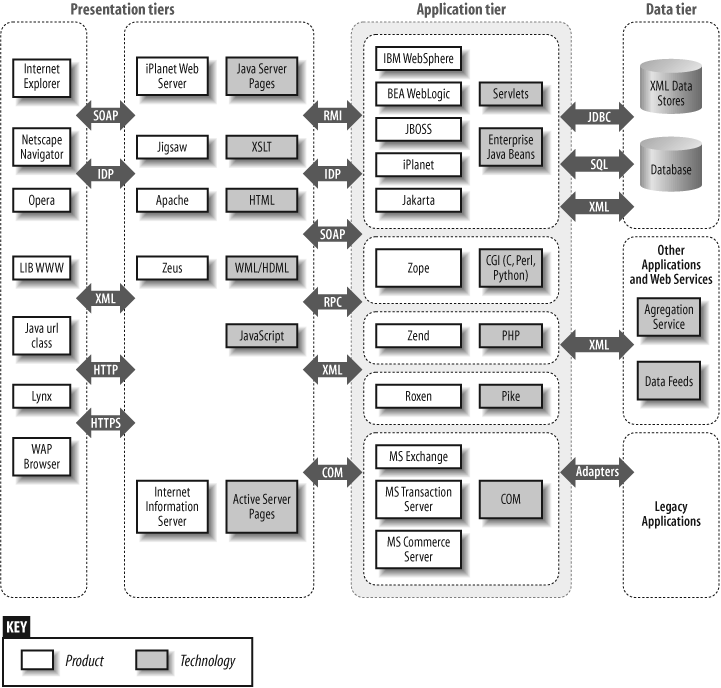
Vulnerabilities can exist in any of these tiers, so it is important to ensure that even small exposures can’t be combined to result in a compromise. From a secure design and development perspective, you must filter and control data flow between the three tiers.
Fingerprinting and assessment of web servers is covered in Chapter 6. In this chapter we detail fingerprinting of application server and backend database components, and assessment ...
Get Network Security Assessment, 2nd Edition now with the O’Reilly learning platform.
O’Reilly members experience books, live events, courses curated by job role, and more from O’Reilly and nearly 200 top publishers.

