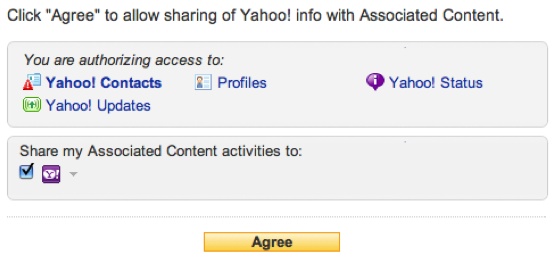
Applications within a social application container do not automatically have access to a user’s social profiles, activity streams, and friendships—that would be a major security concern. Containers usually require that the application define the permission scopes it needs access to. As shown in Figure 1-8, these scopes will be requests that a user must agree to when installing the application.
Typically, social scopes are defined as major pieces of social information about a user, such as his:
Profile
Activity stream
Friendships
Each container may define different scopes or even include a number of nonsocial scopes that a container may gain access to. Once the user accepts the scopes, the container can do things on his behalf. For the three aforementioned social scopes, these things may respectively include:
Allowing the application to capture all information within the user’s profile.
Allowing the application to obtain any activities in the user’s activity stream and to push new activities to this stream on the user’s behalf.
Allowing the application to obtain the profiles for all of the user’s friends. Although those friends have not necessarily added the application, once a user declares that someone is his friend, it establishes a trust relationship, and applications capitalize on this. Essentially, the user trusts that friend with his personal information. When that friend in turn trusts an application with her information, there exists a trust “bridge” between the application and the friends. Some containers impose restrictions on how much social information can be obtained with these predefined trust relationships.
These scopes are usually secured through authorization mechanisms such as OAuth, which require that a user sign in through the container when he grants permissions to an application.
Get Programming Social Applications now with the O’Reilly learning platform.
O’Reilly members experience books, live events, courses curated by job role, and more from O’Reilly and nearly 200 top publishers.