Recipe 7-5: Normalizing Authentication Failure Details
This recipe demonstrates how to modify the authentication response data so that it does not divulge too much information.
Ingredients
- ModSecurity
- SecContentInjection directive
- SecStreamOutbodyInspection directive
- STREAM_OUTPUT_BODY variable
- @rsub operator
Providing Detailed Authentication Failure Information
We don’t need to make an attacker’s job any easier. Unfortunately, that is precisely what we are doing when the login processes on our web applications provide too much information on failed authentication attempts. Two pieces of data usually are required for standard logins: a username and a password.
The attacker must identify the correct combination of these two individual components.
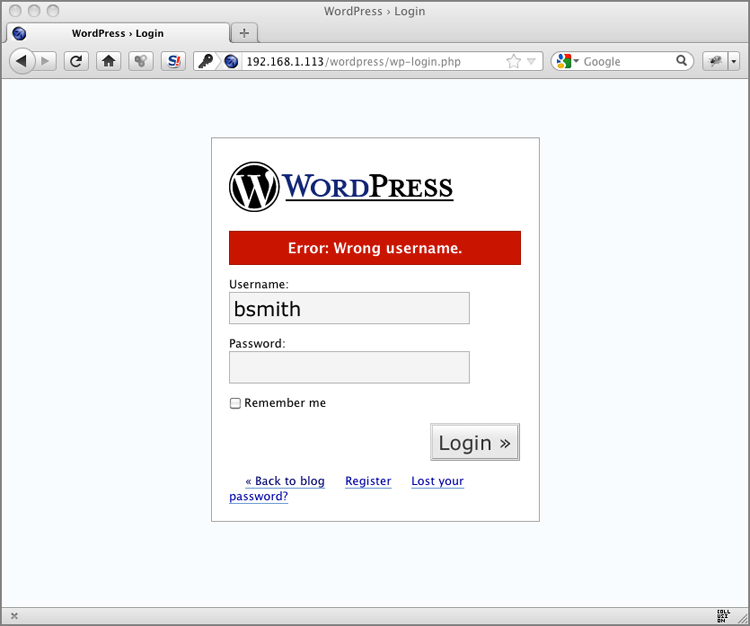
Figure 7-6 shows how WordPress responds when a user submits an authentication attempt with an invalid username.
As you can see, WordPress tells the user that the username is invalid. Knowing this information, an attacker can simply cycle through common usernames or execute a brute-force attack to enumerate valid ones. When a client sends an authentication request with a valid username but an incorrect password, WordPress presents the user with the error page shown in
Figure 7-7.
The error message on this page ...