A manual configuration is generally characterized by a set of proxy addresses, one for each transfer protocol, and a list of domain names for which the proxies should not be used. The set of proxyable transfer protocols includes HTTP, FTP, Gopher, SSL, and WAIS. Usually, a single proxy supports all of these, so the same proxy address is used for all protocols. Some clients allow you to set a single proxy address rather than requiring you to enter the same address repeatedly.
Depending on your reasons for using proxies, you may not need or want to configure all protocols. If your users are behind a firewall, it is probably necessary to proxy all requests. If not, you might want to proxy only HTTP and FTP. A proxy cannot cache SSL responses because the content is encrypted. Forwarding SSL requests when the client can make a direct connection serves only to increase the load upon the proxy. Gopher and WAIS requests might be cachable, but they typically comprise such a small fraction of total traffic that the cache provides relatively little benefit.
The manual configuration approach has a number of disadvantages. Primarily, it requires a significant amount of individual effort to enter all the settings. Knowledgeable users may not be bothered, but a typical user requires very clear and specific instructions. Additionally, you may need to provide different instructions for different browsers and different versions of the same browser. Another annoyance is that the manual configuration results in poor failover characteristics. When a proxy fails, the browser does not attempt a direct connection or try an alternate proxy. Arguably, browsers should support this feature, but at the time of this writing, they do not. Finally, a manual configuration is not flexible enough to accommodate systems with multiple proxy machines. For example, you might want to forward one class of requests to one proxy and the remaining traffic to another.
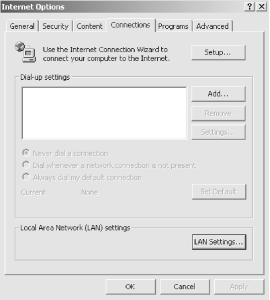
To configure Microsoft Internet Explorer Version 5, select View → Internet Options from the menu. This brings up a new window with six “tabs” along the top. Select the Connection tab and you will see the window shown in Figure 4-1. The proxy settings are buried under LAN Settings…, so click on that button and you should see the window shown in Figure 4-2.
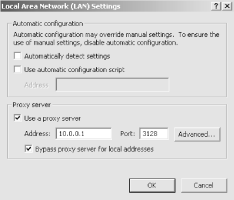
The LAN Settings window has a subwindow titled Proxy server. Here you can enter an IP address or hostname and the proxy port number. This configures Internet Explorer to use the proxy for all transfer protocols.
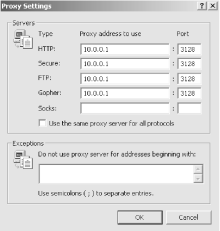
If you want to use different proxies or no proxy for some protocols (such as FTP or SSL), click on the Advanced… button. Now you should see the window shown in Figure 4-3. You can enter hostnames or IP addresses for each transfer protocol separately. Note that “Secure” refers to SSL. You can enter a list of domain names in the Exceptions subwindow. URLs that match these domains are not sent to your proxies. With Internet Explorer, you must separate domains with semicolons instead of commas. When you finish configuring the proxies, be sure to return to the browser and try a new request.
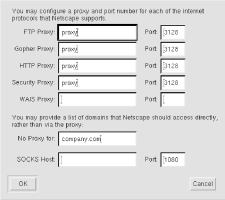
Netscape’s browser products allow you to set proxy addresses in pop-up windows. To bring up the configuration window in Netscape Navigator Version 4, select Edit → Preferences… from the main menu bar. In the Preferences window, click on the small triangle next to Advanced. This adds two more entries to the menu, one of which is Proxies. Next, select Manual proxy configuration and click on the View… button. You should now see the window shown in Figure 4-4.
Once you have the manual proxy configuration window, you can enter proxy addresses. Usually, you enter the same proxy address for every protocol (HTTP, FTP, Gopher, Wais). Security Proxy refers to SSL (a.k.a. HTTPS) requests. SSL requests are never cached by proxies, so the only reason to configure an SSL proxy is to tunnel through a firewall. Do not set the SSL proxy if you are not behind a firewall. In the No Proxy for field, you can enter a comma-separated list of domains that should not be requested through the proxy. When you are finished, return to the main browser window by clicking the OK button, and then try to load a new URL.
Note that Netscape hasn’t changed the proxy configuration in the newer versions of Navigator. The windows may look a little bit different, but the pull-down menus and text boxes are the same for Version 6.
Unix-based clients such as NCSA Mosaic for X, Lynx, and Wget look for proxy addresses in environment variables. Note that the variable names are lowercase. For historical reasons, these environment variables look just like URLs:[19]
http_proxy="http://squid.nlanr.net:3128/" ftp_proxy="http://squid.nlanr.net:3128/"
These clients also look for environment variables named gopher_proxy, https_proxy, and wais_proxy.
The no_proxy variable holds URL domain names that should not be forwarded to the proxy. In most cases, this includes your local domain (or domains). To specify multiple domains, simply separate them with commas. For example:
no_proxy="nlanr.net,sdsc.edu"
Netscape Navigator for Unix actually reads these environment variables as well, but only if the user’s preferences file does not exist.
[19] This is because very early proxies simply prepended these proxy URLs to the original URL and then processed the request normally.
Get Web Caching now with the O’Reilly learning platform.
O’Reilly members experience books, live events, courses curated by job role, and more from O’Reilly and nearly 200 top publishers.