Auditing Shares
Shares, particularly user-configured shares, can be a source of insecure computing. Therefore, it is incumbent upon network administrators to periodically audit shares on both workstations and servers to ensure that only authorized, properly configured shares are in use.
Depending on your auditing needs, you may inspect shares by producing a report from the Access database examined earlier in this chapter to save your share information. Such a report is shown in Figure 5-8.
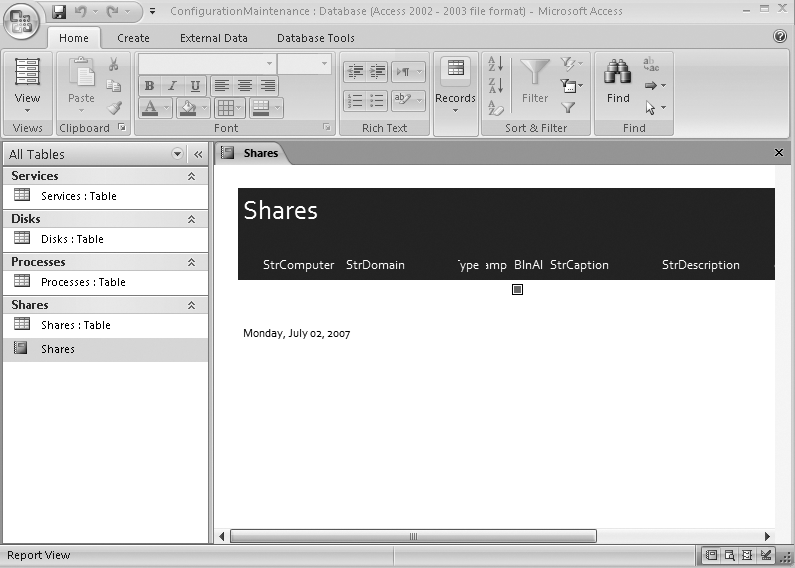
Figure 5-8. One of the strengths of Access is the ease of creating reports, such as this Shares report.
Another way to audit shares is to maintain a text file that ...
Get Windows PowerShell™ Scripting Guide now with the O’Reilly learning platform.
O’Reilly members experience books, live events, courses curated by job role, and more from O’Reilly and nearly 200 top publishers.

