Visual Traffic Analysis with Ethereal
Sift through network data with one of the most advanced protocol analyzers available.
Ethereal is
one of the most popular protocol analyzers on the planet. It runs on
virtually all major platforms, including Linux, BSD, Mac OS X, and
Windows. Like tcpdump
[Hack #37], it
can capture packets
directly from a network interface, or analyze data from a previously
saved file. While capturing data, Ethereal can give you
real-time
statistics about which protocols are actively in use (Figure 3-35). Start capturing by selecting
Capture
→
Start..., select the interface you want to
capture from, and click OK. Note that you need
proper permissions (typically root privileges) to actually capture
data.
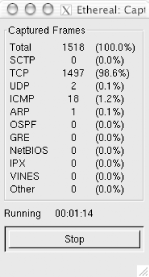
Figure 3-35. Ethereal gives you statistics about the protocols it sees as it captures packets.
If you would like to see these statistics again (with even more
detail) after you have finished capturing packets, go to
Tools
→
Protocol Heirarchy
Statistics. You can use this on previously captured dump
files as well. If you already have some captured data (say, saved
with tcpdump from a remote machine), you can simply click
File
→
Open... and
select the file you’d like to analyze.
Ethereal displays the data it has collected in three ways. The top part of the window shows a summary of the data, with one packet per line. This lists the sequence, time, IP data, protocol, ...
Get Wireless Hacks now with the O’Reilly learning platform.
O’Reilly members experience books, live events, courses curated by job role, and more from O’Reilly and nearly 200 top publishers.

