Okta app for SAML and SCIM
Please reach out to your customer success manager to get started. They’ll connect you with a member of the O’Reilly integration team who’ll configure the O’Reilly side of the integration while you configure your end in Okta.
Prerequisites
Please be sure you have the following before you begin updating your Okta tenant with SAML and/or SCIM.
- Ability to install a new app from the Okta Integration Network (OIN) on your production Okta tenant
- For SAML single sign-on: SSO connection name (provided by your O’Reilly customer success manager or the O’Reilly integration team)
- For SCIM provisioning: SCIM API token (obtained from the Integrations page of your Admin Console)
- For SCIM provisioning: Completed prerequisites for adding SCIM to Okta
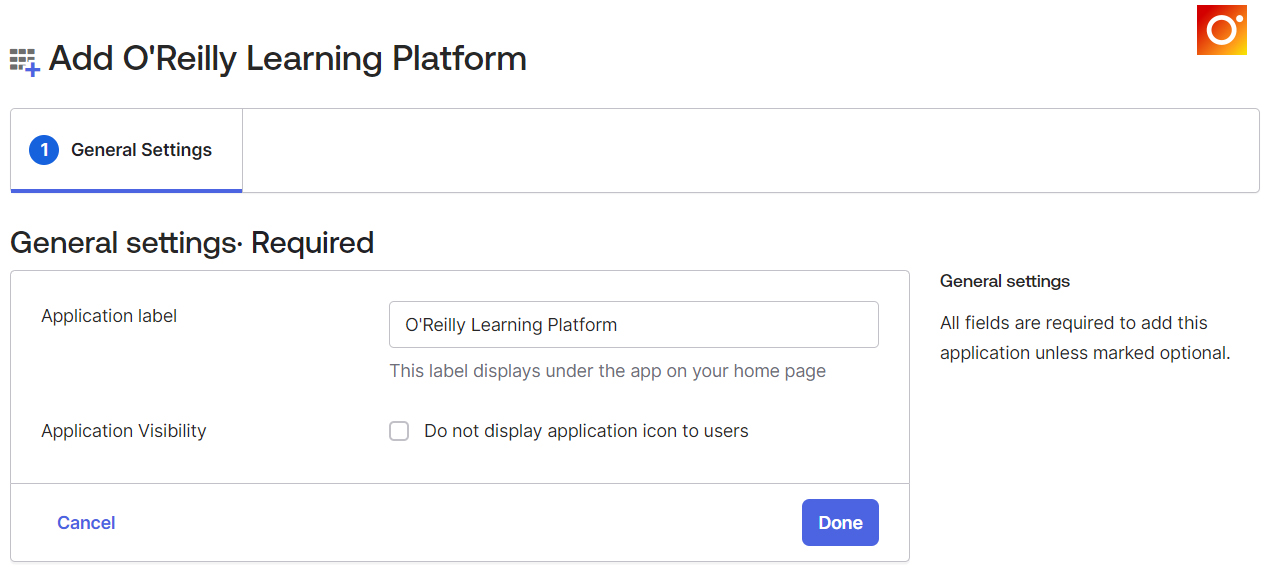
Add O’Reilly’s Okta app
-
Add the O’Reilly Learning Platform app from the Okta Integration Network to your Okta tenant by clicking +Add Integration.
-
Change the Application Visibility setting to hide this app from users if desired. (Optional)
-
Click Done to add the yet-unconfigured app to your Okta tenant. Then follow the steps below to finish setting up SAML, SCIM, or both.
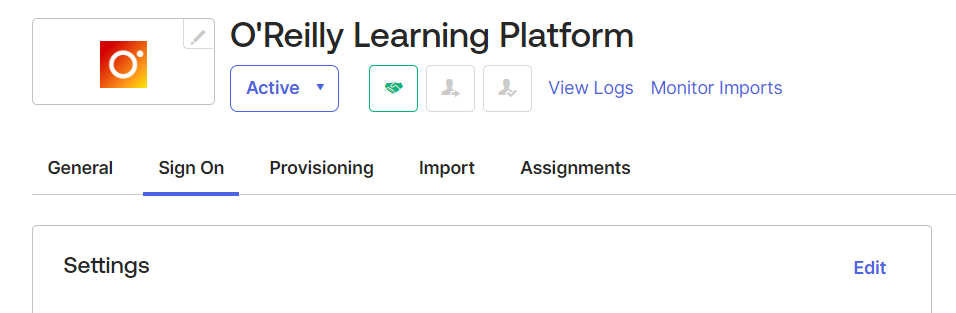
Implement SSO using Okta with SAML
-
In Okta, navigate to the Sign On tab and click Edit in the top right corner. The app has been preconfigured to use SAML 2.0 as the sign-on method.
-
Scroll down to Advanced Sign-on Settings and enter the provided Connection Name. If you haven’t received your SSO connection name, please contact your customer success manager.

-
If you won’t be using SCIM with Okta for provisioning and are using Okta’s default for usernames (email), change the Application username format to be a unique and stable identifier. This allows us to automatically update users’ email addresses whenever they change in Okta. If your user directory integration does not provide a suitable identifier, we recommend Okta’s internal user profile id. To use this identifier, select Custom and enter the following expression: user.getInternalProperty("id")

-
-
Click Save, then scroll down to SAML Signing Certificates. In the table (seen below), open the Actions menu and select View IdP metadata.

-
Send the URL that appears in the browser to the (or save the metadata XML file and email it to them as an attachment). From there, you’ll work together to test and finalize the integration.

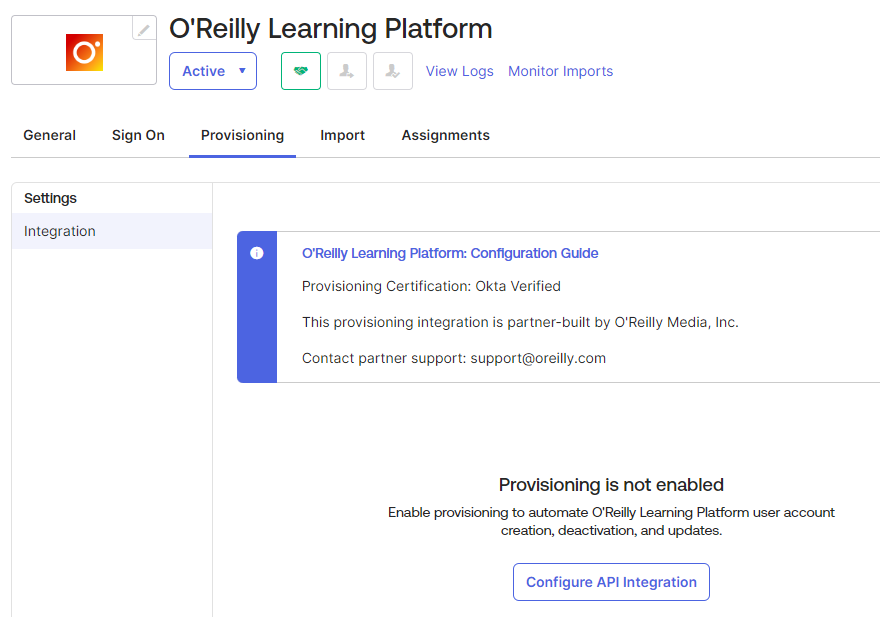
Add SCIM for user provisioning to your Okta integration
Supported features
The Okta-to-O’Reilly SCIM integration supports the following features:
- Create Users: A user will be created in the O’Reilly platform when you assign them to the O’Reilly Learning Platform application in Okta.
- Update User Attributes: When you change a user’s name or email address in Okta, these changes will be pushed to the O’Reilly learning platform. We support the following attributes: userName, email, givenName, and familyName.
- Deactivate Users: If you deactivate a user or unassign the application in Okta, the user’s access to the O’Reilly learning platform will be revoked. This will also remove O’Reilly account manager privileges from a user who has that role.
- Reactivate Users: If you reactivate a user or reassign the application in Okta, the user’s access to the O’Reilly learning platform will be restored. Account manager privileges are not automatically restored upon reactivation; they must be requested from your customer success manager.
For more information on the listed features, visit the Okta Glossary and the O’Reilly Admin Glossary.
Configuration steps
-
Before setting up SCIM, verify that your organization meets the requirements for adding SCIM to Okta.
-
To get started, use the token creator on the Integrations page of your Admin Console to generate the required SCIM API token. If you don’t have access or if you run into any issues, please reach out to your customer success manager.
-
Save the provided SCIM API Token value in your password manager or other secure location.
-
In Okta, navigate to the Provisioning tab in the O’Reilly Learning Platform application and click the Configure API Integration button.
-
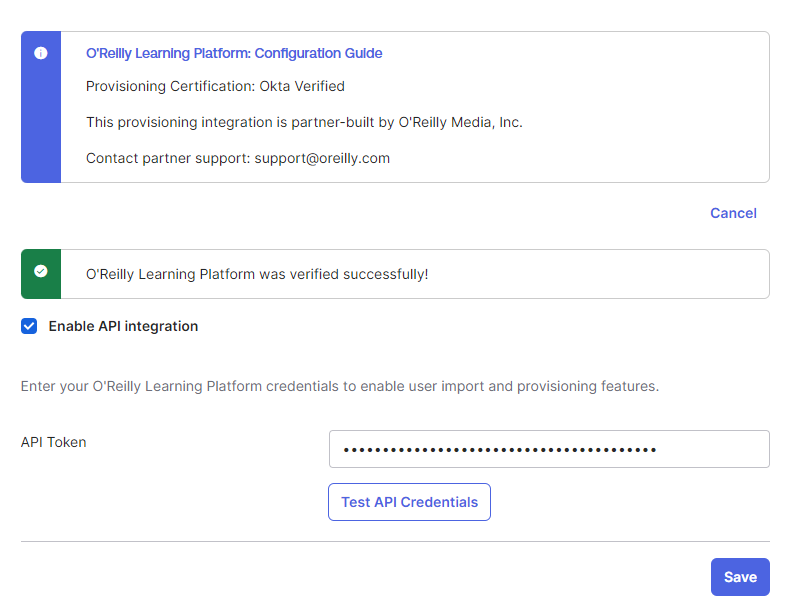
Select the checkbox next to Enable API integration.
-
Enter the SCIM API Token from step 3 in the corresponding field.
-
Click the Test API Credentials button. If you receive an error, verify that your credentials are entered correctly.
-
Upon a successful test, click Save.
-
-
Please ensure that all users who should have access to O’Reilly have been assigned this app in Okta, especially the users who are O’Reilly account managers. Continuing with the next step will remove access from any active O’Reilly users who have not been assigned this app in Okta.
-
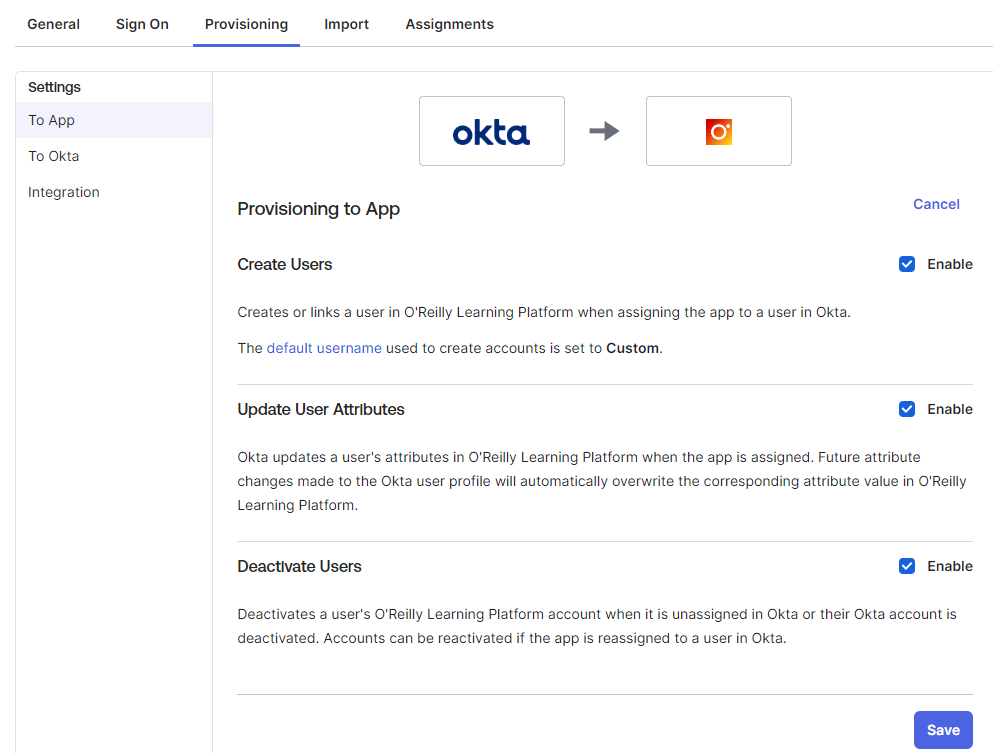
In Okta, while still on the Provisioning tab, click To App in the left navigation and then click Edit.
-
Choose from the following functions the O’Reilly SCIM API can support in Okta. (We recommend selecting all three).
- Create Users: A user will be created in the O’Reilly learning platform when you assign them to the O’Reilly Learning Platform application in Okta.
- Update User Attributes: When you change a user’s name or email address in Okta, these changes will be pushed to the O’Reilly learning platform.
- Deactivate Users: If you remove permission for a user in Okta, the user will be updated to “revoked” status in the O’Reilly learning platform. This will also remove O’Reilly account manager privileges from a user who has that role.
-
Enable each provisioning operation to be used by checking the corresponding Enable checkbox, then click Save at the bottom of this section.
-
And you’re done! Okta now controls which users are active in the O’Reilly learning platform.
Notes
- Users who have been deactivated using SCIM will not be able to log in by any means while inactive.
- Okta provides features that can help automate app assignments based on user or group information and your business rules. In addition, if Okta’s Self Service request feature is enabled, it’s possible to let users request access to O’Reilly right in Okta by configuring an approval workflow for the O’Reilly app.
SAML and SCIM support
If you have any questions during or after the integration, please reach out to your customer success manager or the O’Reilly integration team at