CHAPTER 1Introduction to Social Engineering and Phishing
Chapter 1 is going to discuss the importance of fighting social engineering and phishing. If you have to persuade your boss or colleagues why fighting against these threats matters, this chapter is for you.
What Are Social Engineering and Phishing?
I think everyone knows what phishing is. It's hard to go an entire day without being exposed to it in some way. It's everywhere! We know it when we see it. Most of us are exposed to it daily, or nearly daily, usually through scam emails, text messages, or calls to our cell phones. Figure 1-1 shows a representative common example of a phishing email.
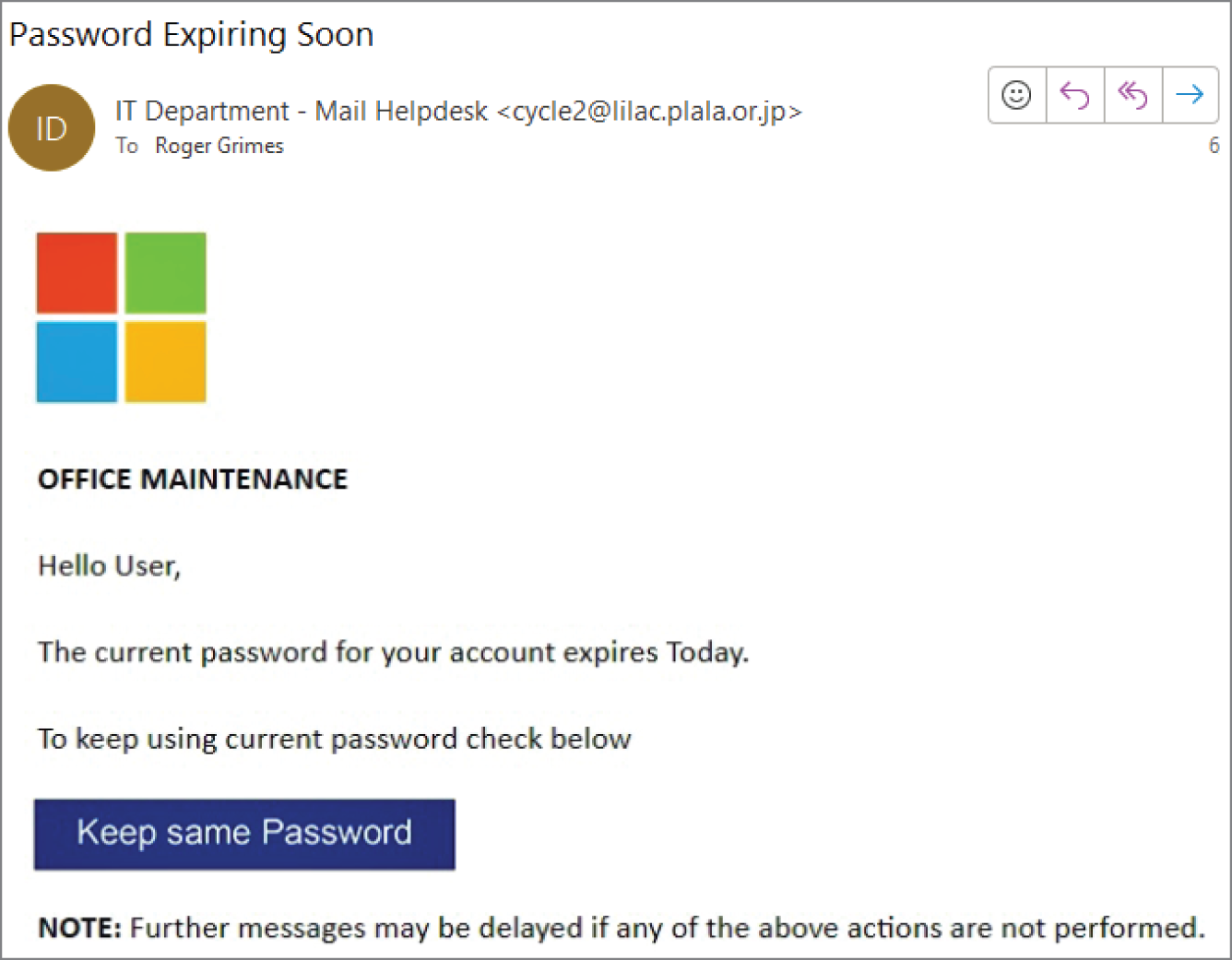
FIGURE 1-1 Common type of phishing email.
Figure 1-1 is an example of a very common type of phishing email, likely the most common, where the phisher is attempting to make it look like an official email from Microsoft asking for an account password. If a victim were to click on the ”Keep same Password” button, they would be directed to a fake, look-alike website asking for the victim to input their real account password. There are many classic signs of this being a phishing email, which we will be discussing in more detail in future chapters, but the most obvious is that the originating email address comes from some random email address from Japan (as indicated by the domain suffix of .jp) and is not microsoft.com as would ...
Become an O’Reilly member and get unlimited access to this title plus top books and audiobooks from O’Reilly and nearly 200 top publishers, thousands of courses curated by job role, 150+ live events each month,
and much more.
Read now
Unlock full access