August 2018
Intermediate to advanced
254 pages
6h 20m
English
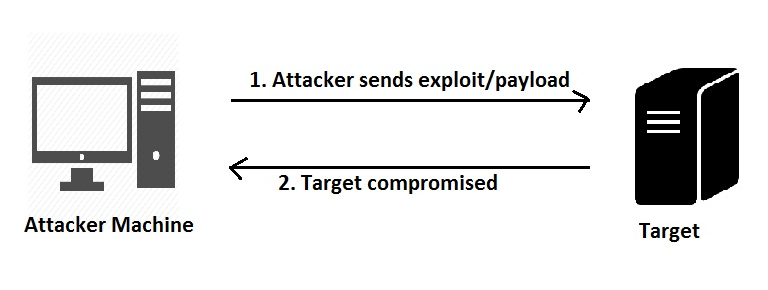
In this type, the attacker has direct access to the target system. The attacker essentially knows the IP address of the target system and connects to it remotely. The attacker then exploits an existing vulnerability on the target system which gives further access.
Read now
Unlock full access