August 2018
Intermediate to advanced
254 pages
6h 20m
English
Before we go ahead and exploit the services on remote target system, we must know what all the services are running and what their exact versions are. We can do a quick Nmap scan to list service version information as shown in the following image:
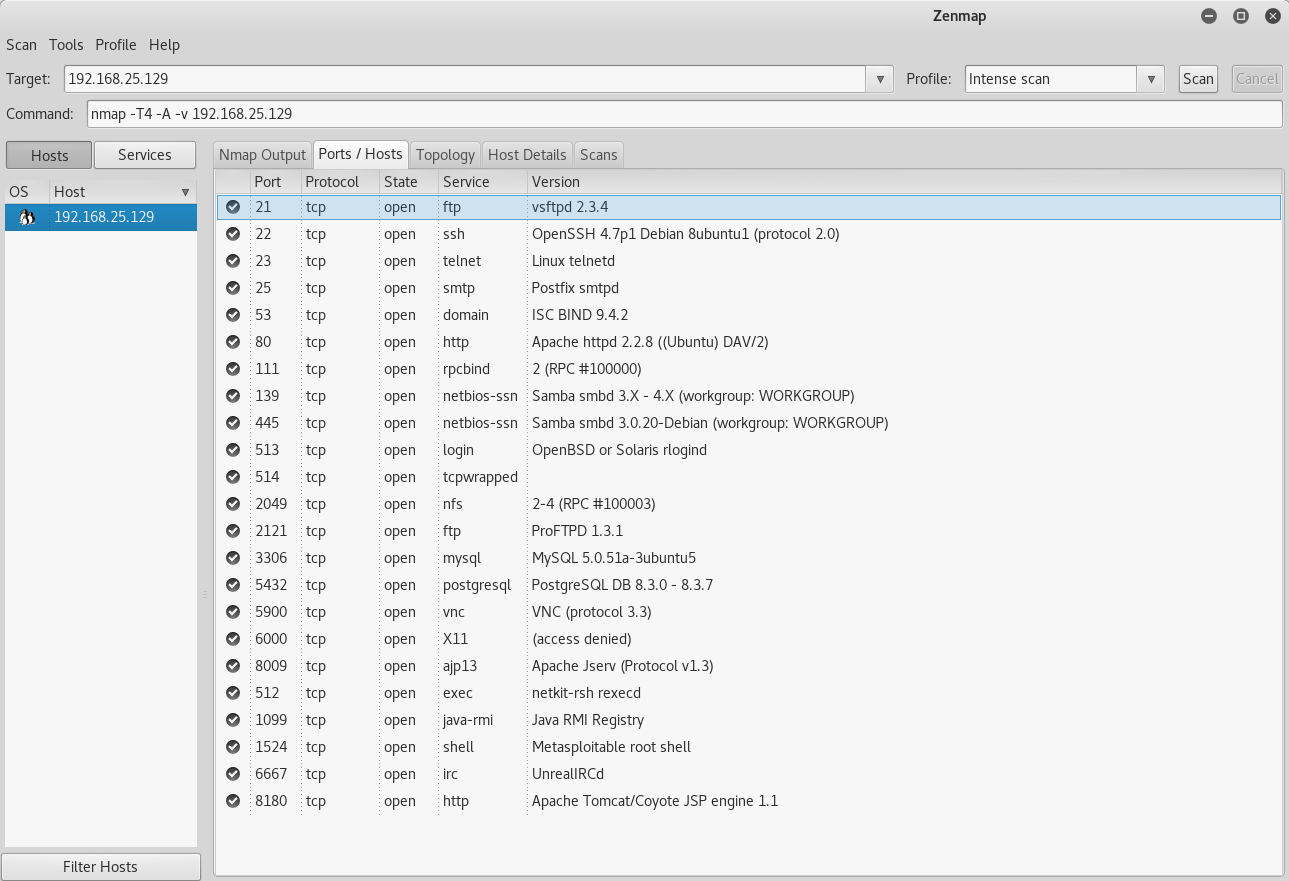
The preceding result shows there are many services running which we can exploit using Metasploit.
Read now
Unlock full access