2 IBM Business Process Manager Security: Concepts and Guidance
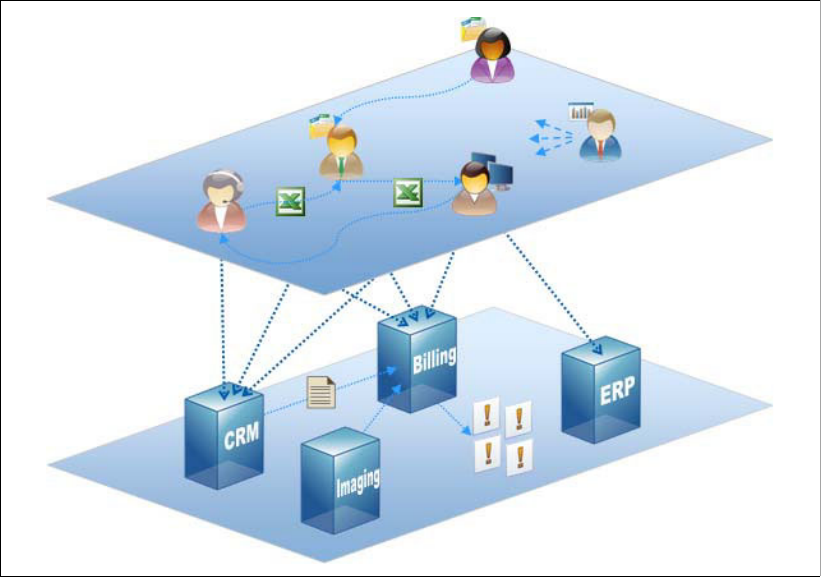
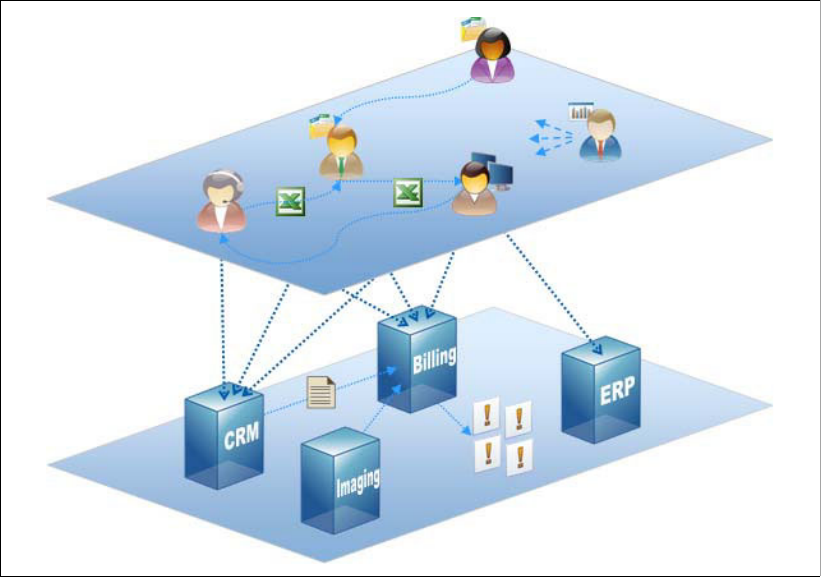
1.1 BPM is your corporate DNA
Before we get started with the details, it is worth considering the fundamental need for
securing your BPM systems. First of all, we acknowledge that IBM Business Process
Manager is based upon Java 2 Enterprise (J2E) technologies, and is delivered largely
through HTTP protocols, and so it therefore has the same security requirements as any other
J2E enterprise-ready application. Authentication, authorization and protection of sensitive
data are all topics that are common to any J2E application, and so many casual observers
may stop their inquiry there ...