Chapter 3. Authentication: Who has access 59
The bottom line, as mentioned in the previous chapter, is to eliminate the “low hanging fruit”.
Encrypt the communications channels, and eliminate the possibility of these types of attacks
before the opportunity arises.
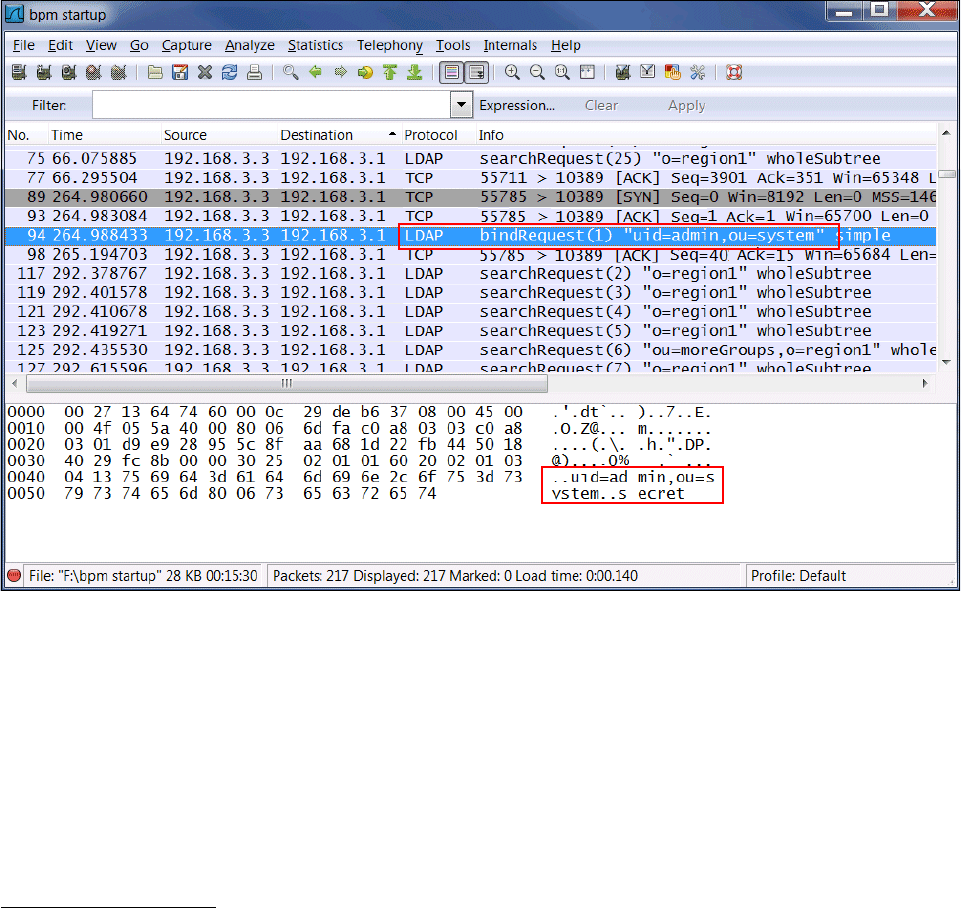
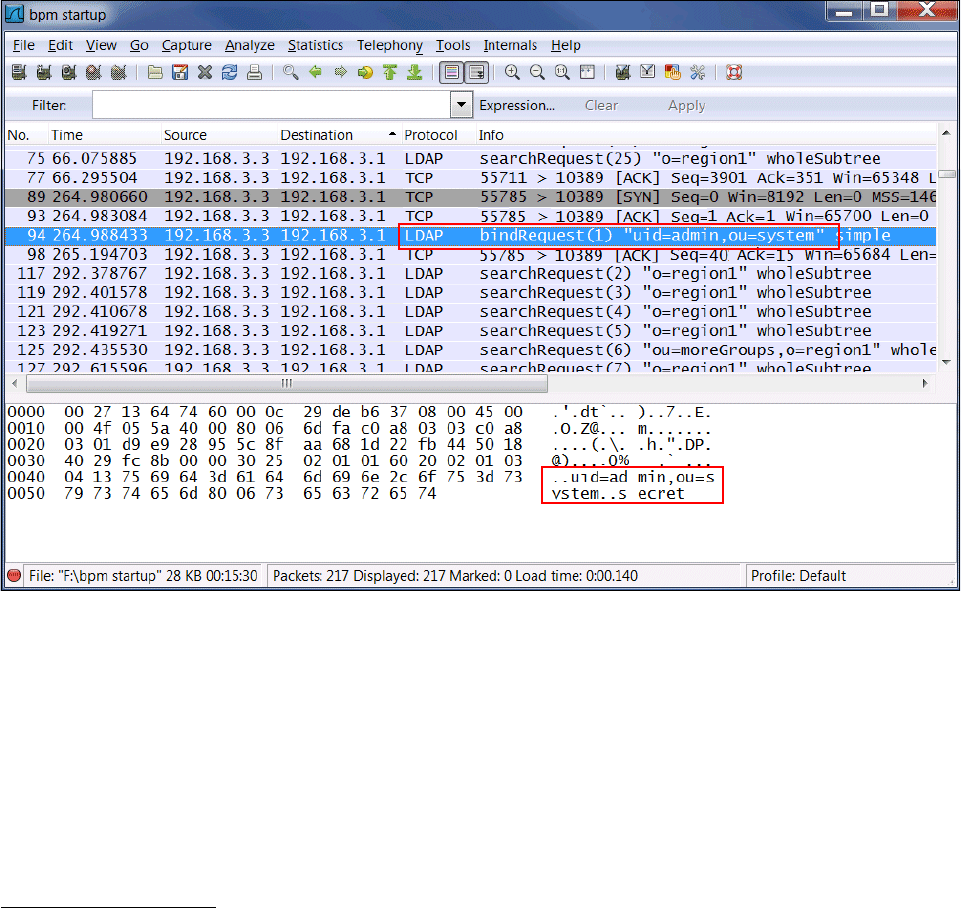
3.3.4 Insecure LDAP connections
Most people think of LDAP as a server, but in fact LDAP stands for Lightweight Directory
Access Protocol. Yes, there are LDAP servers, but it is helpful to keep in mind that it is
fundamentally a protocol—which means, in effect, that this is a conversation between two
servers.
As another specific example of how an overabundant faith in firewalls can be ...